Security and Compliance: Overview
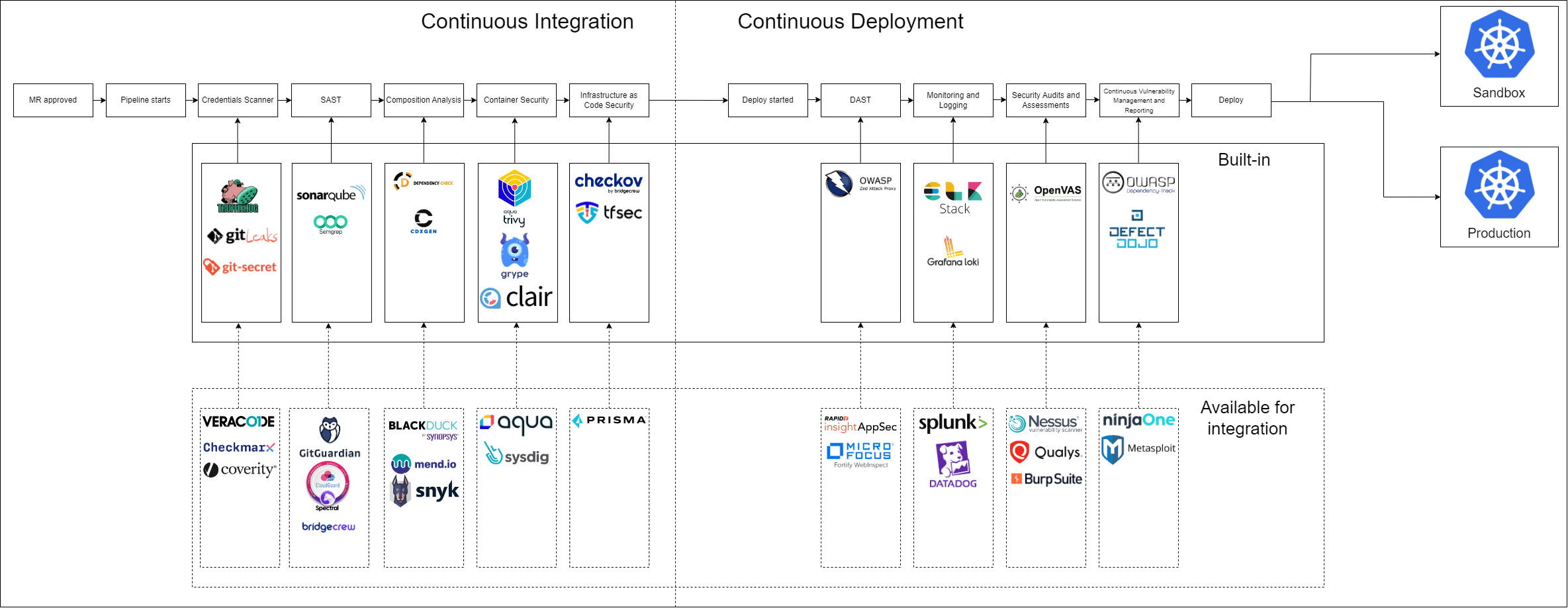
KubeRocketCI emphasizes the importance of incorporating security practices into the software development lifecycle through the DevSecOps approach. By integrating a diverse range of open-source and enterprise security tools tailored to specific functionalities, organizations can ensure efficient and secure software development. These tools, combined with fundamental DevSecOps principles such as collaboration, continuous security, and automation, contribute to the identification and remediation of vulnerabilities early in the process, minimizes risks, and fosters a security-first culture across the organization.
Integrated Scanners
The following tools are built into KubeRocketCI Tekton pipelines and run automatically as part of CI/CD workflows. For detailed information on when each scanner runs, how reports are produced, and how data flows into DefectDojo and Dependency-Track, refer to the Security Scanning Pipelines page.
| Tool | Category | Runs In | Results Destination |
|---|---|---|---|
| SonarQube | SAST + Code Quality | Build and Review pipelines | SonarQube server |
| Semgrep | SAST | Security-Scan pipeline | DefectDojo |
| Gitleaks | Secret Detection | Security-Scan pipeline | DefectDojo |
| CycloneDX cdxgen | SCA / SBOM Generation | Security-Scan pipeline | Dependency-Track |
| Trivy | Container Vulnerability Scan | Security-Scan, Image-Scan-Remote pipelines | DefectDojo |
| Anchore Grype | Container Vulnerability Scan | Security-Scan pipeline | DefectDojo |
| Hadolint | Dockerfile Linting | Review pipelines | Pipeline log |
| Helm chart-testing | Helm Chart Linting | Review pipelines | Pipeline log |
Required Integrations
To enable the full security scanning stack, provision the following integration secrets. Each secret is optional — if missing, the corresponding scanning step is skipped gracefully, allowing incremental tool adoption.
| Secret | Keys | Integration Guide |
|---|---|---|
ci-sonarqube | token, url | SonarQube Integration |
ci-defectdojo | token, url | Integrate DefectDojo |
ci-dependency-track | token, url | Integrate Dependency-Track |
Supported Solutions Catalog
Beyond the tools integrated into default pipelines, KubeRocketCI supports the integration of additional open-source and enterprise security tools for organizations with extended security requirements. The table below provides a comprehensive view of available options for each security aspect.
| Functionality | Open-Source Tools (integrated in Pipelines) | Enterprise Tools (available for Integration) |
|---|---|---|
| Hardcoded Credentials Scanner | TruffleHog, GitLeaks, Git-secrets | GitGuardian, SpectralOps, Bridgecrew |
| Static Application Security Testing | SonarQube, Semgrep CLI | Veracode, Checkmarx, Coverity |
| Software Composition Analysis | OWASP Dependency-Check, cdxgen | Black Duck Hub, Mend, Snyk |
| Container Security | Trivy, Grype, Clair | Aqua Security, Sysdig Secure, Snyk |
| Infrastructure as Code Security | Checkov, Tfsec | Bridgecrew, Prisma Cloud, Snyk |
| Dynamic Application Security Testing | OWASP Zed Attack Proxy | Fortify WebInspect, Rapid7 InsightAppSec, Checkmarx |
| Continuous Monitoring and Logging | ELK Stack, OpenSearch, Loki | Splunk, Datadog |
| Security Audits and Assessments | OpenVAS | Tenable Nessus, QualysGuard, BurpSuite Professional |
| Vulnerability Management and Reporting | DefectDojo, OWASP Dependency-Track | Metasploit |
Tool Descriptions
Vulnerability Management
DefectDojo is a comprehensive vulnerability management and security orchestration platform facilitating the handling of uploaded security reports. Examine the prerequisites and fundamental instructions for installing DefectDojo on Kubernetes or OpenShift platforms.
OWASP Dependency-Track is an intelligent Software Composition Analysis (SCA) platform that provides a comprehensive solution for managing vulnerabilities in third-party and open-source components. See the integration guide for setup instructions.
Source Code Security
Semgrep CLI is a versatile and user-friendly command-line interface for the Semgrep security scanner, enabling developers to perform Static Application Security Testing (SAST) for various programming languages. It focuses on detecting and preventing potential security vulnerabilities, code quality issues, and custom anti-patterns.
Gitleaks is a versatile SAST tool used to scan Git repositories for hardcoded secrets, such as passwords and API keys, to prevent potential data leaks and unauthorized access.
TruffleHog is an open-source tool designed for finding and identifying potentially sensitive and secret information in the source code and commit history of Git repositories.
Git-secrets is an open-source tool that helps prevent the accidental committing of secrets, sensitive information, and other types of confidential data into Git repositories.
Container Security
Trivy is a simple and comprehensive vulnerability scanner for containers and other artifacts, providing insight into potential security issues across multiple ecosystems. Trivy can be seamlessly integrated into CI/CD pipelines or utilized as part of Harbor.
Grype is a fast and reliable vulnerability scanner for container images and filesystems, maintaining an up-to-date vulnerability database for efficient and accurate scanning.
Clair is an open-source container security tool designed to help assess the security of container images and identify vulnerabilities within them.
Software Composition Analysis
Cdxgen is a lightweight and efficient tool for generating Software Bill of Materials (SBOM) using CycloneDX, a standard format for managing component inventory. It helps organizations maintain an up-to-date record of all software components, their versions, and related vulnerabilities.
OWASP Dependency-Check is a software composition analysis tool that helps identify and report known security vulnerabilities in project dependencies.
Infrastructure as Code Security
Tfsec is an effective Infrastructure as Code (IaC) security scanner, tailored specifically for reviewing Terraform templates. It helps identify potential security issues related to misconfigurations and non-compliant practices.
Checkov is a robust static code analysis tool designed for IaC security, supporting various IaC frameworks such as Terraform, CloudFormation, and Kubernetes. It assists in detecting and mitigating security and compliance misconfigurations.
Dynamic Application Security Testing
OWASP Zed Attack Proxy (ZAP) is a security testing tool for finding vulnerabilities in web applications during the development and testing phases.
Monitoring and Logging
ELK Stack (Fluent Bit, Elasticsearch, Kibana) is used in Kubernetes for log aggregation, supporting Logsight for Stage Verification and Incident Detection.
Loki is a log aggregation system designed for cloud-native environments. It is part of the CNCF and is often used alongside Prometheus for monitoring and observability.
OpenSearch is the flexible, scalable, open-source way to build solutions for data-intensive applications.
Security Audits
OpenVAS is an open-source network vulnerability scanner and security management tool designed to identify and assess security vulnerabilities in computer systems, networks, and applications.