Guide: Microsoft Entra SSO Integration With OpenSearch
This guide provides instructions on how to configure OpenSearch with OpenID Connect (OIDC) authentication using Microsoft Entra as the Identity Provider (IdP).
Prerequisites
Before you begin, make sure the following prerequisites are met:
- Access to the Microsoft Entra Admin Center with administrative privileges.
- Microsoft Entra Tenant is created.
- OpenSearch is installed (can be installed during Configuring Helm chart step).
- A forked copy of the edp-cluster-add-ons repository is created.
- (Optional) External Secrets Operator is installed.
Configuring Microsoft Entra Application
To configure Microsoft Entra as the Identity Provider for OpenSearch, it is necessary to create and configure an Application in the Microsoft Entra Admin Center:
-
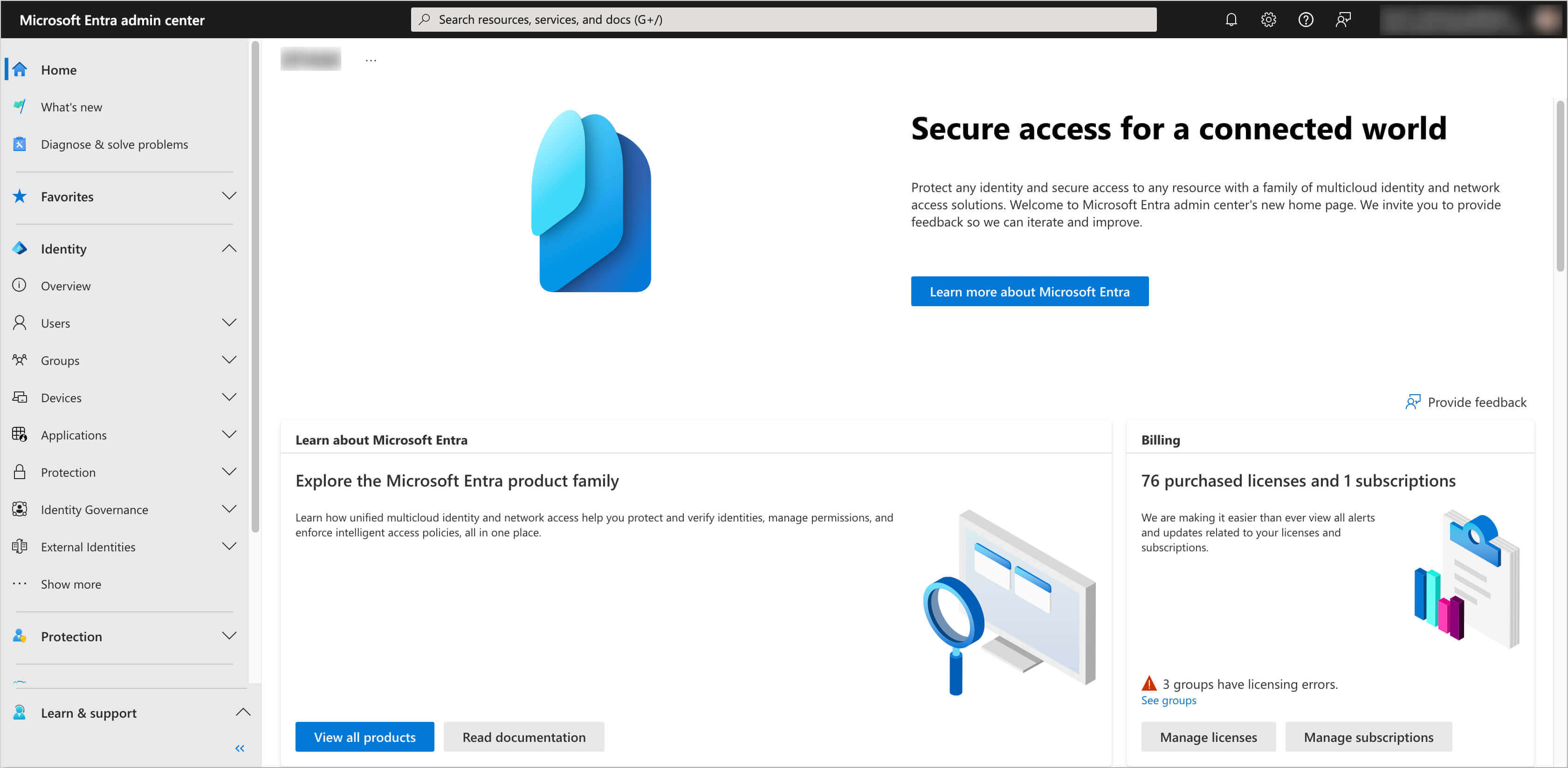
Log in to the Microsoft Entra Admin Center:
-
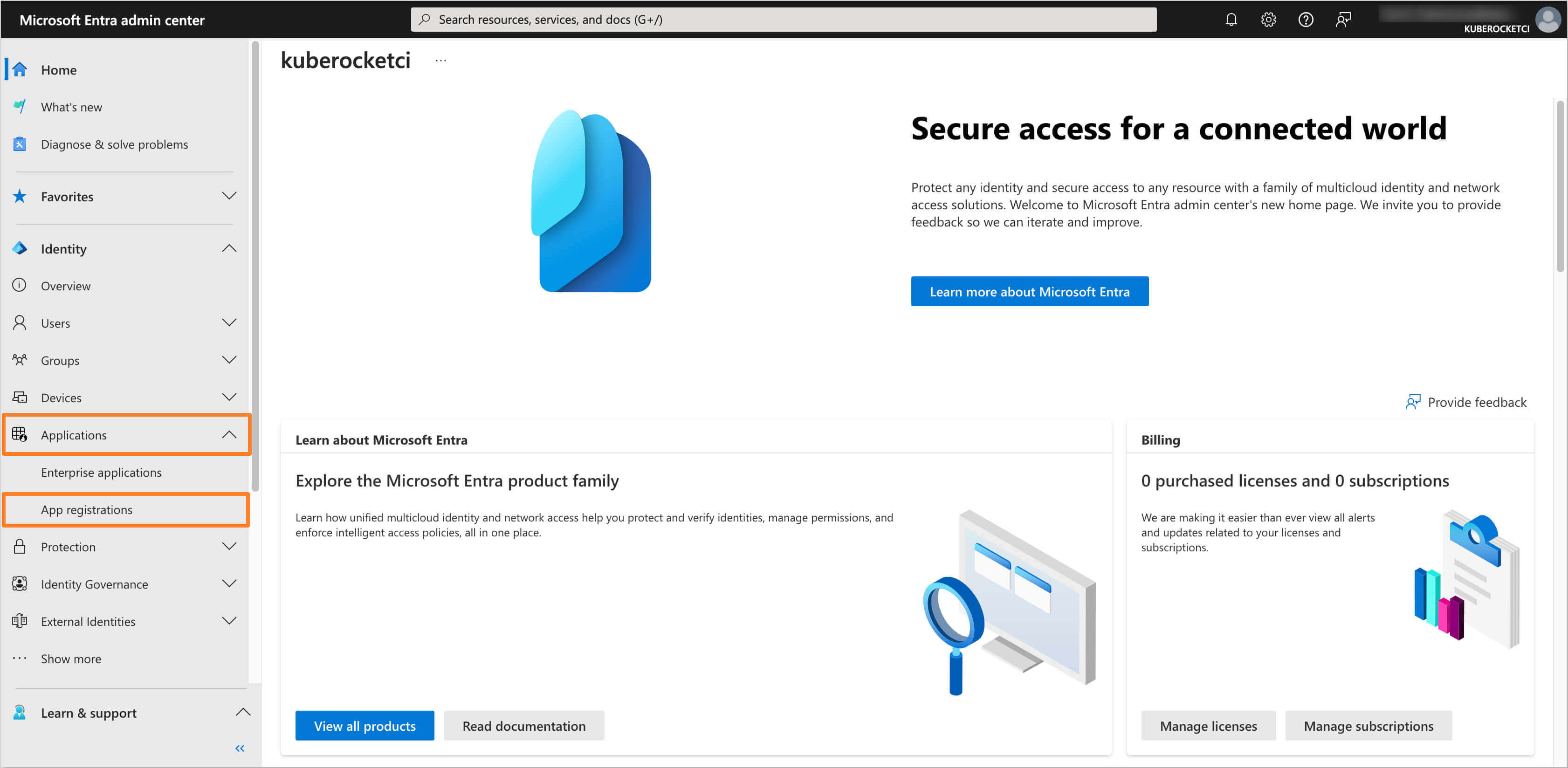
In the left sidebar menu, select Applications and click App registrations:
-
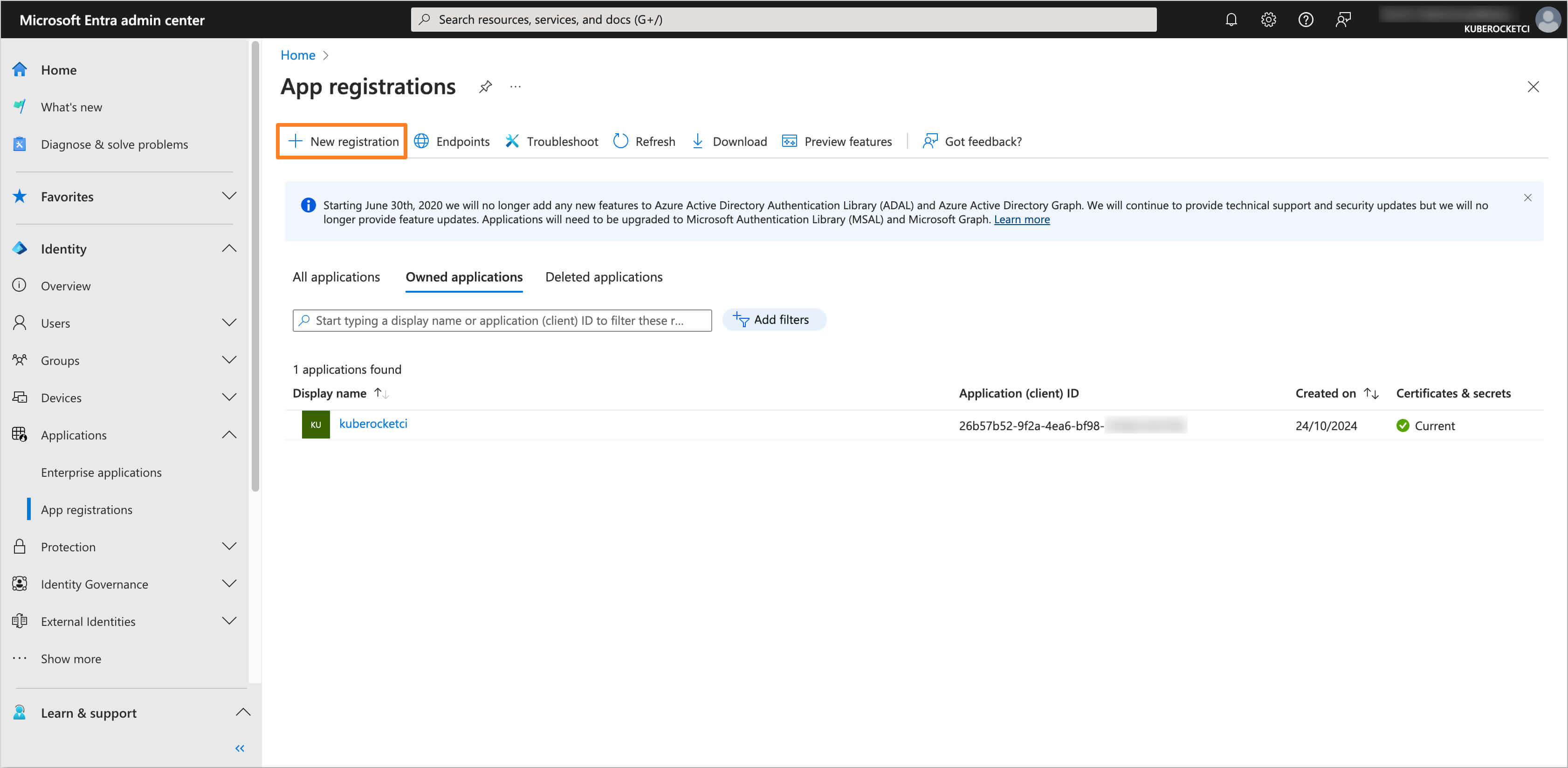
Click on the New registration button:
-
Fill in the required fields, such as Name, Supported account types and Redirect URI (You can skip setting the Redirect URI if you don't deploy OpenSearch yet). Click Register to create the application:
noteThe Redirect URI should be in the format
https://<OpenSearch Dashboard URL>/auth/openid/login.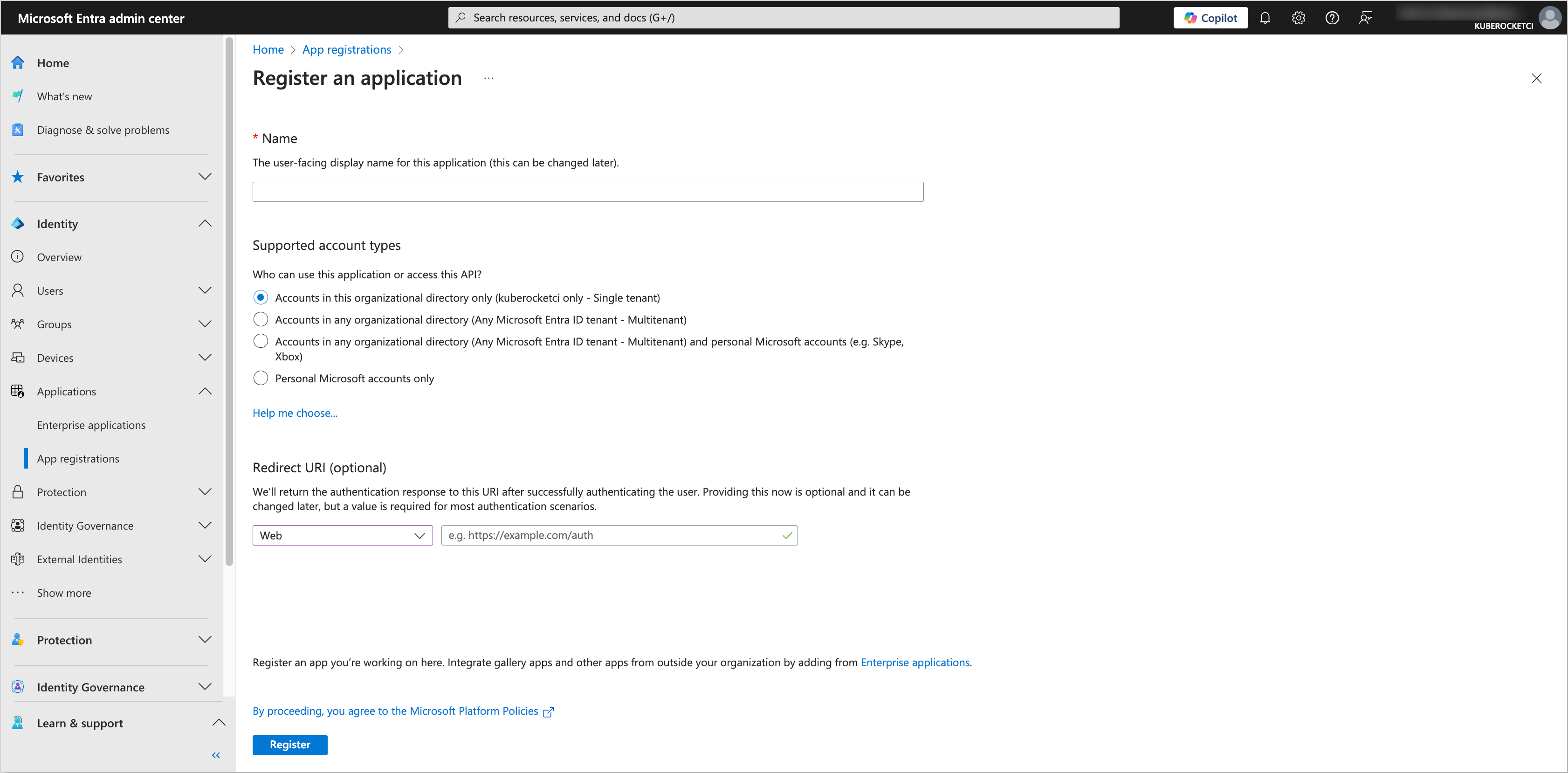
-
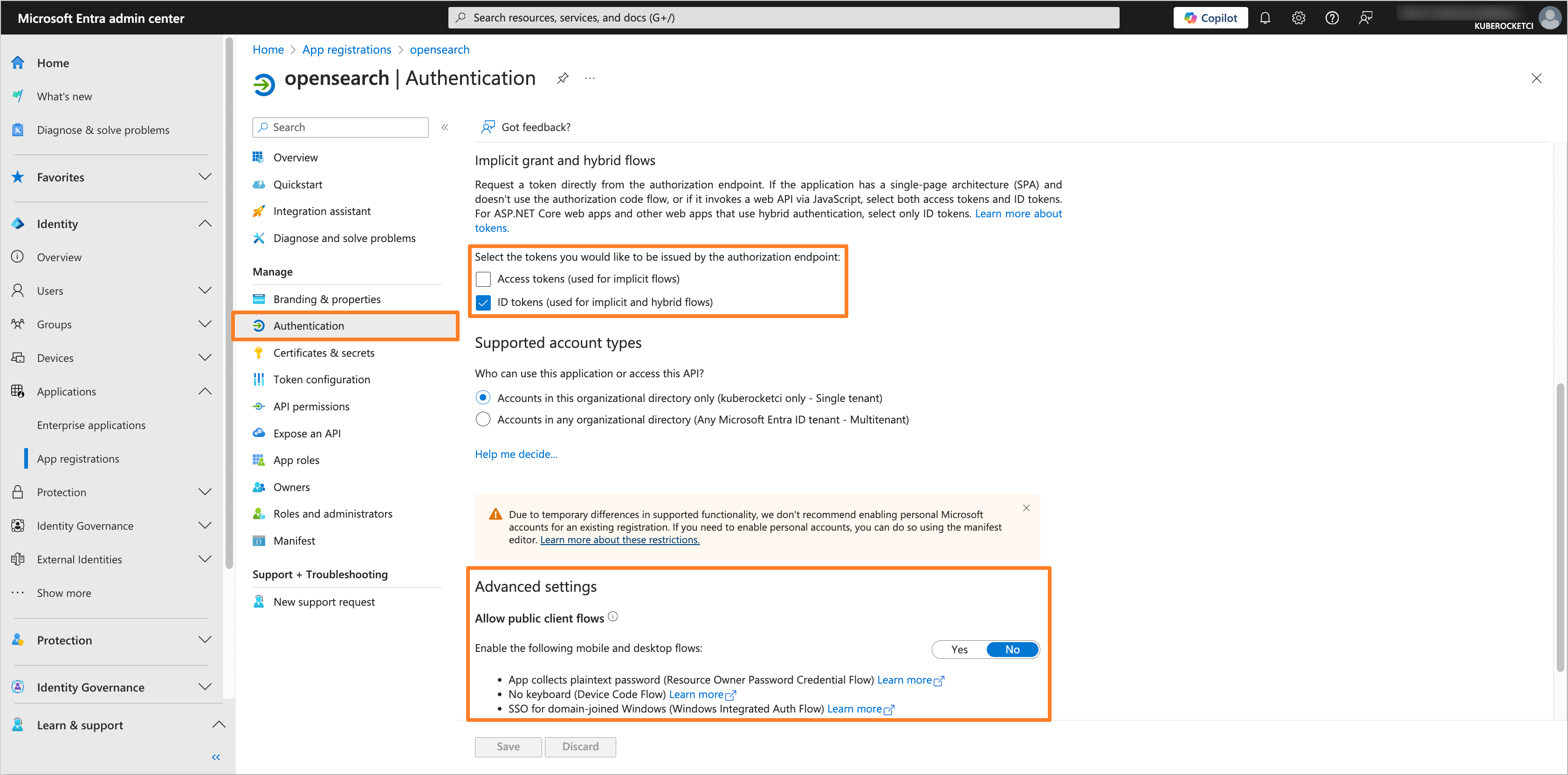
In the created application, navigate to the Authentication section from the left sidebar menu. In the Implicit grant and hybrid flows section, select ID tokens for the token type. In the Allow public client flows section, set the value to No:
-
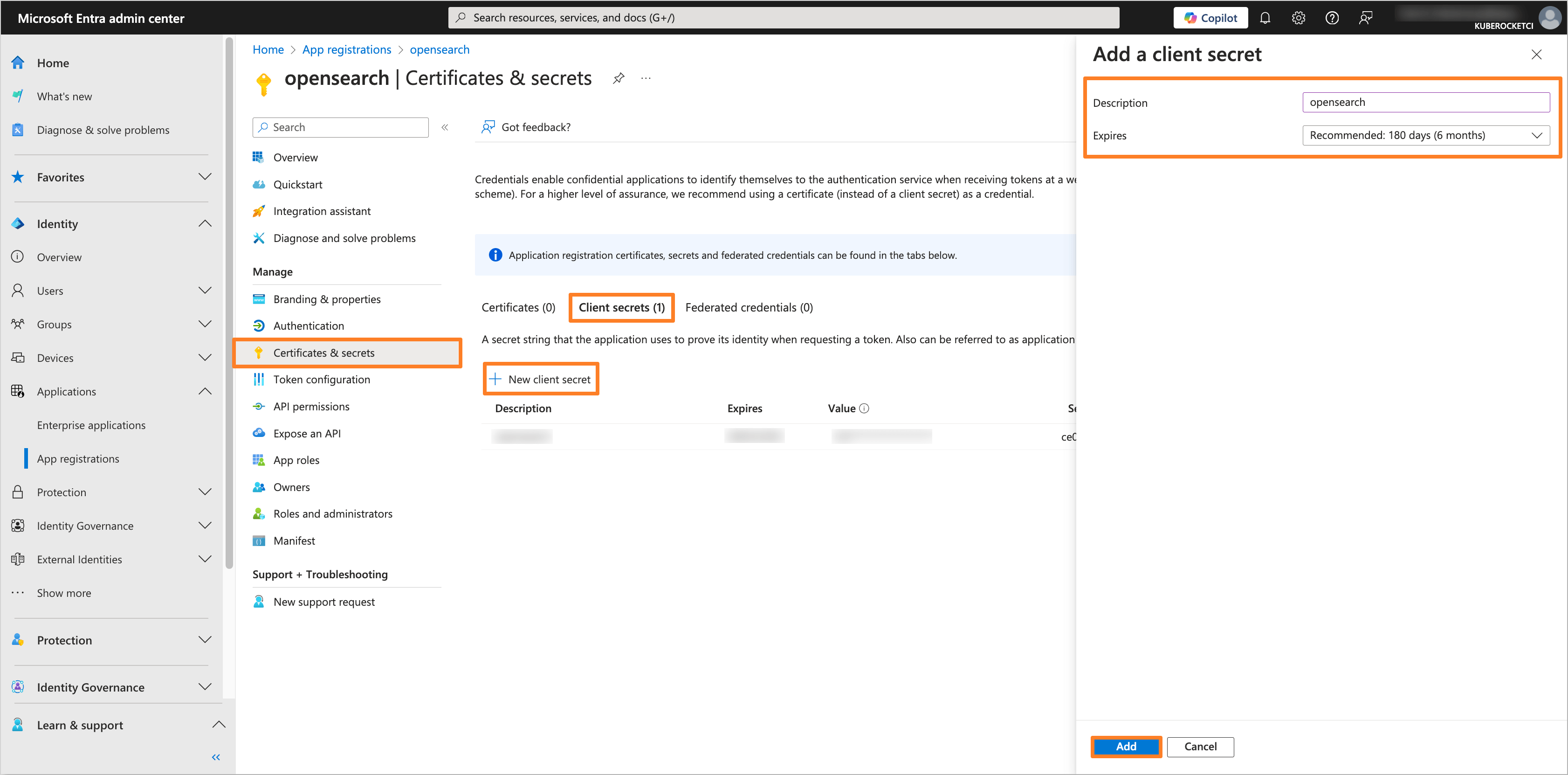
Navigate to the Certificates & secrets section. In the Client secrets tab, click on the New client secret button to create a new secret. Fill in the required fields and click Add:
-
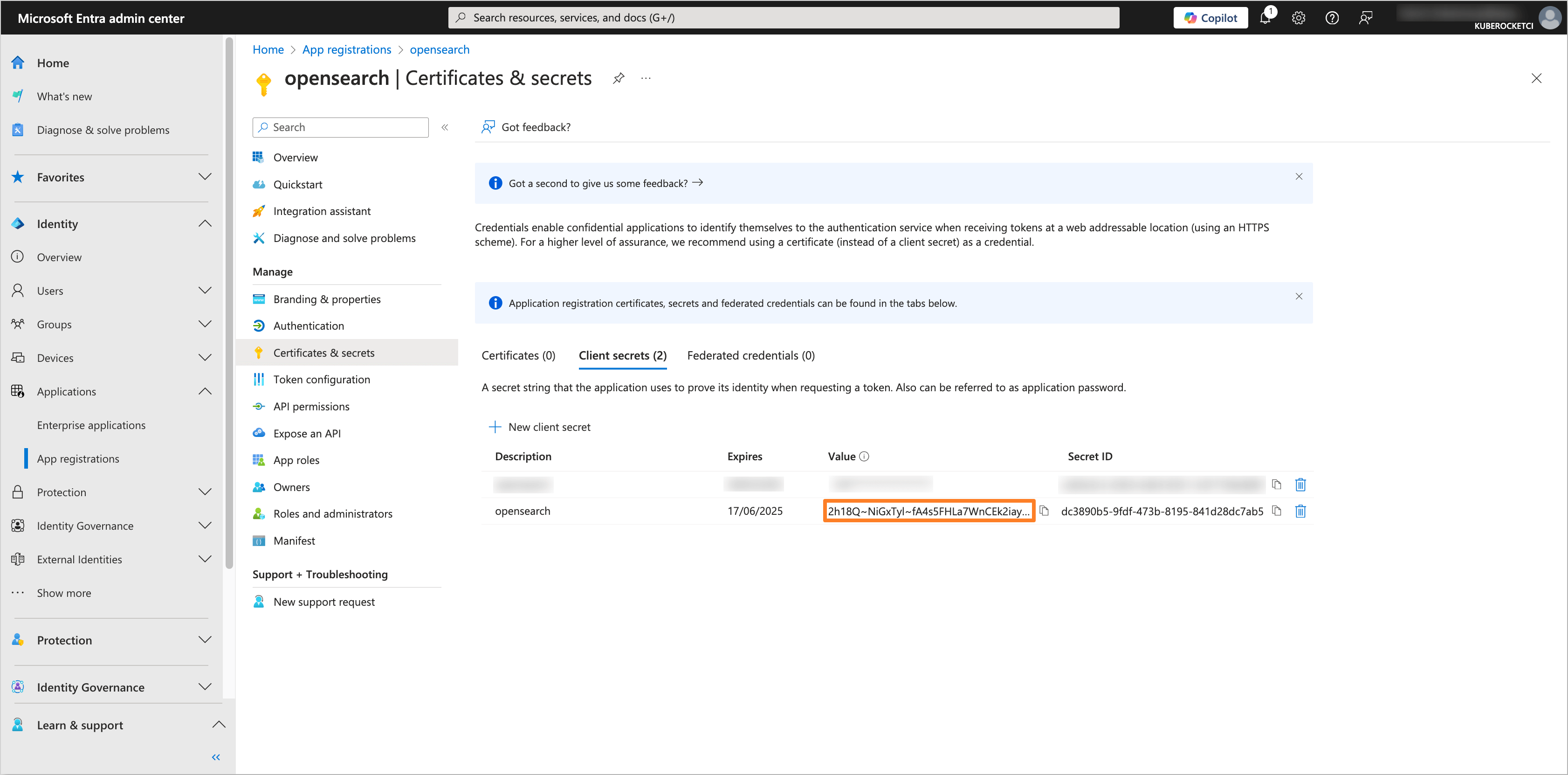
Copy the generated client secret value and store it securely. You will need this value to configure the OpenSearch Helm chart:
-
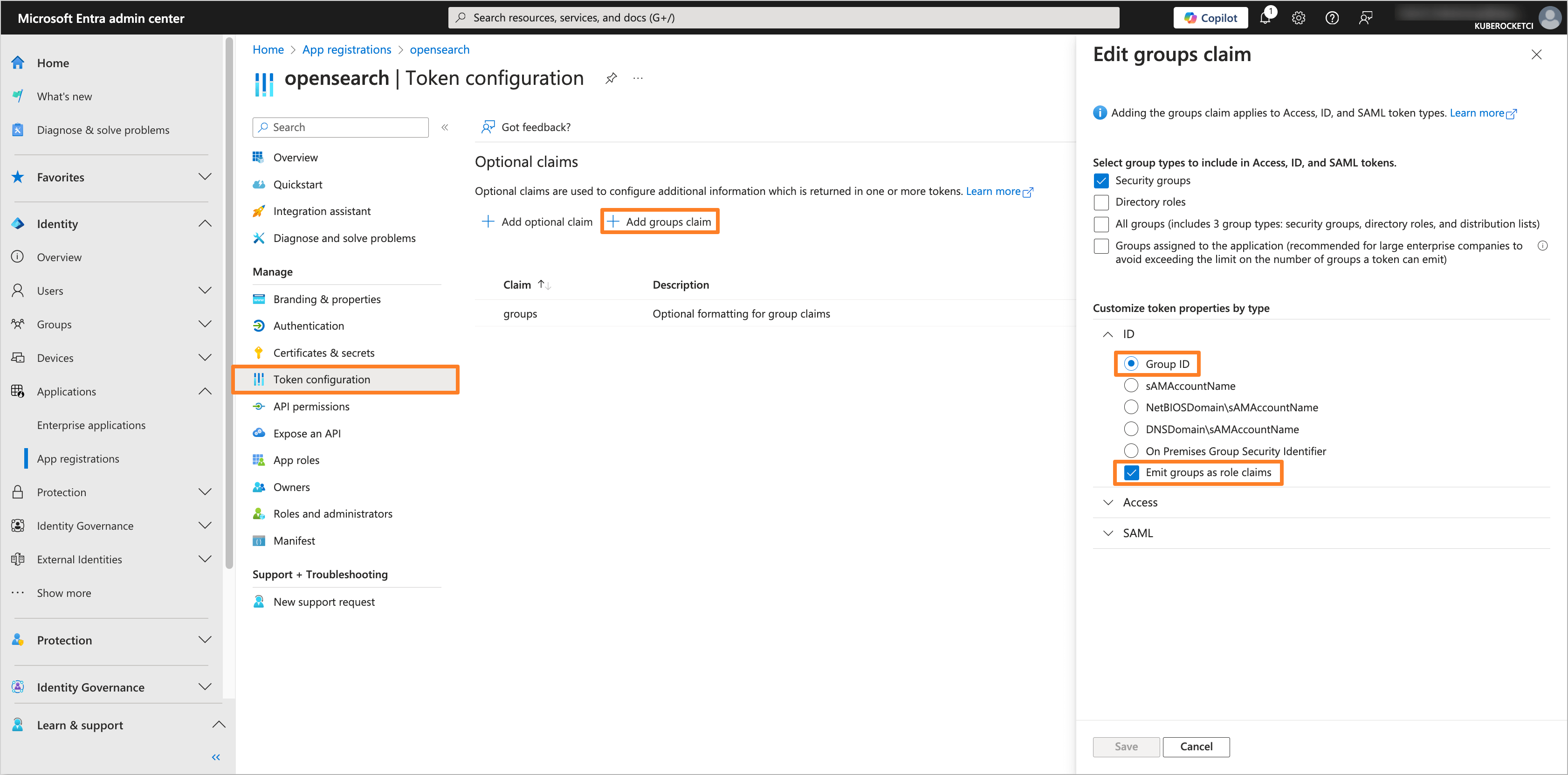
Navigate to the Token configuration section and click on Add groups claim button. Choose the group type as Security Groups and for the ID token type, select Group ID. Also, choose the Emit groups as role claims option:
-
Navigate to the API permissions section. Click on the Add a permission button. Select Microsoft Graph and then Delegated permissions. Add the following permissions:
- openid
- profile
- User.Read
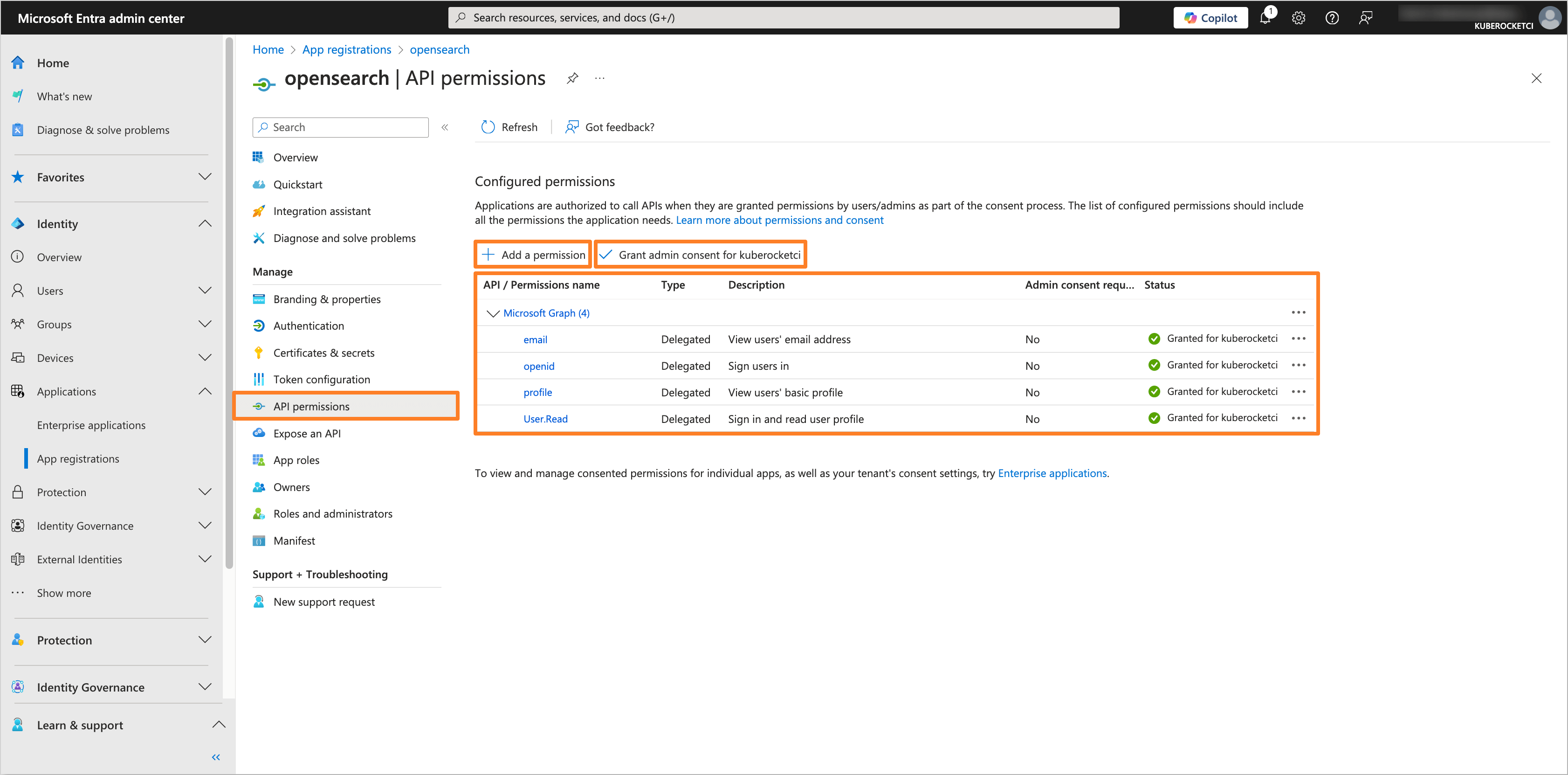
After adding the permissions, click on the Grant admin consent for 'Tenant name' button to grant the required permissions.
After configuring the Microsoft Entra Application, you can proceed with the OpenSearch configuration.
Creating the Groups
To manage access to OpenSearch, it is necessary to create the groups in Microsoft Entra and assign users to it.
-
In the Microsoft Entra Admin Center, in the left sidebar menu, select Groups and then All groups. Click on New group button to create a new group(s) for users who will have access to OpenSearch (e.g.,
administrator,developer):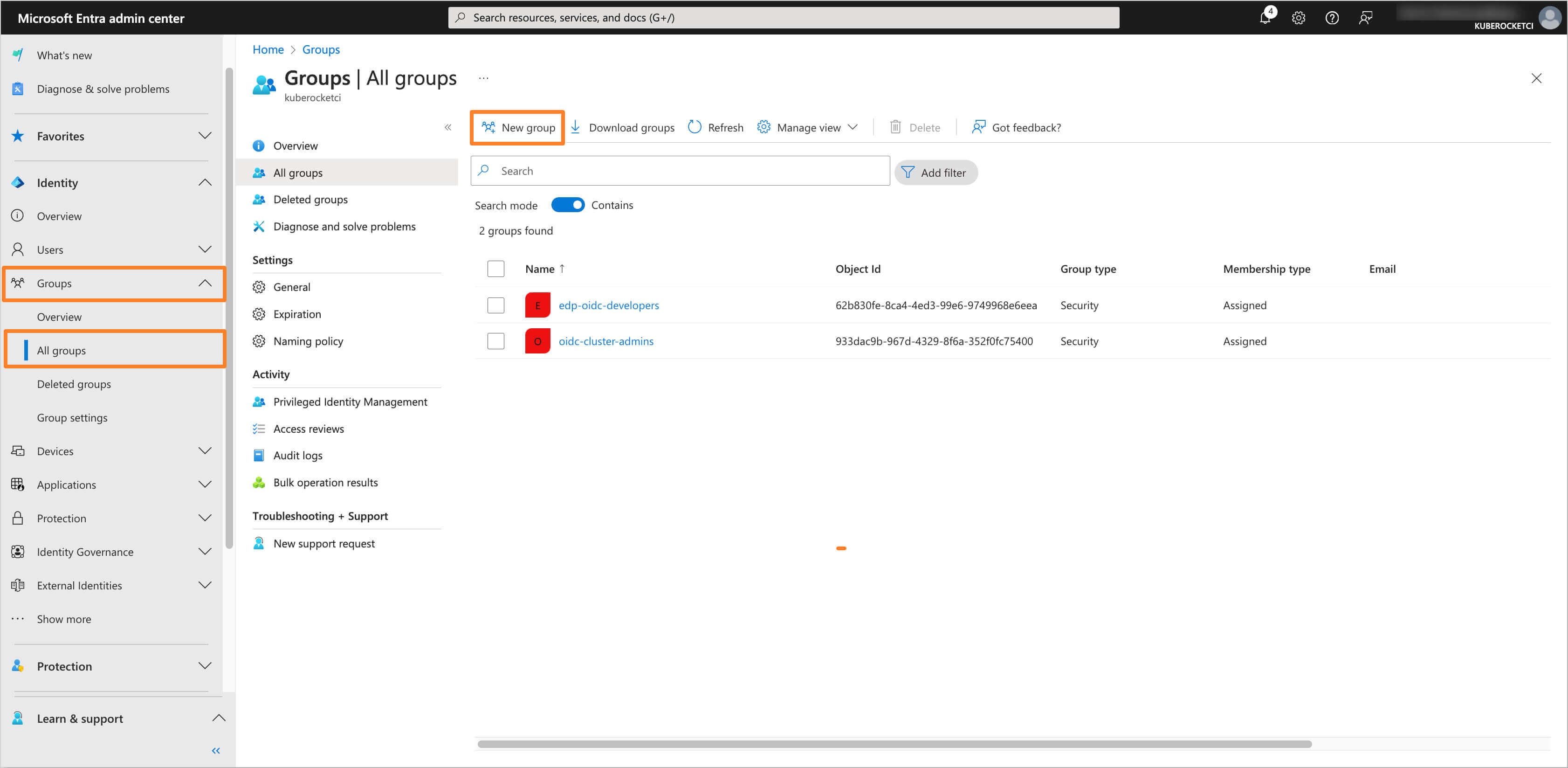
-
Fill in the required fields, such as Groups type and Group name. In the Members section, add users who will be part of the group:
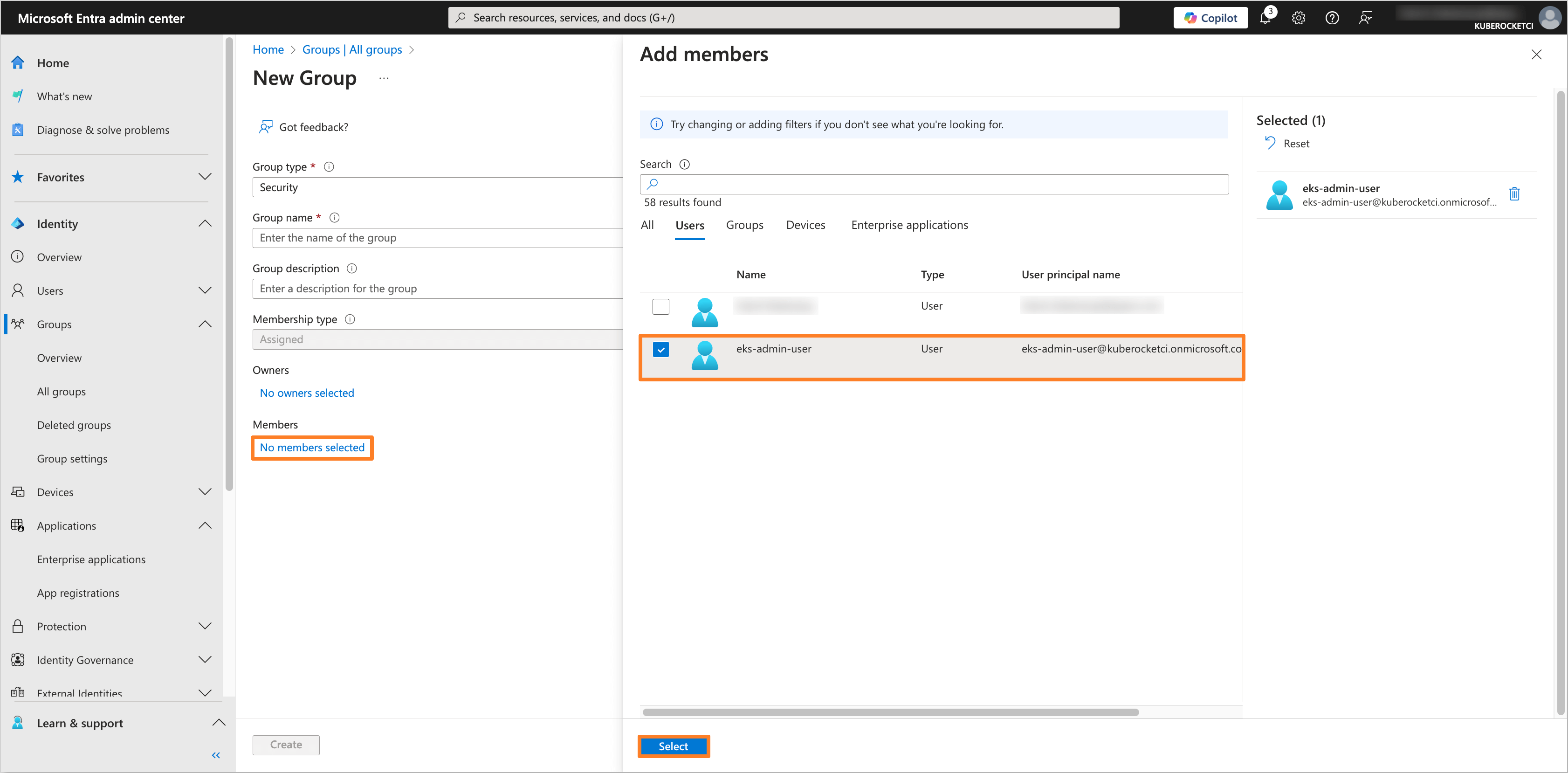
-
After adding the necessary members, review the group settings and click Create to save the group. Repeat this process for each required group.
Configuring OpenSearch Helm chart
To integrate OpenSearch with configured Microsoft Entra Application, it is necessary to configure the OpenSearch Helm chart. In this example, we will use the edp-cluster-add-ons repository to deploy OpenSearch to the Kubernetes (e.g. AWS EKS) cluster.
The Application data, such as Application (client) ID and Directory (tenant) ID, can be found in the Overview section of the Application in the Microsoft Entra Admin Center.
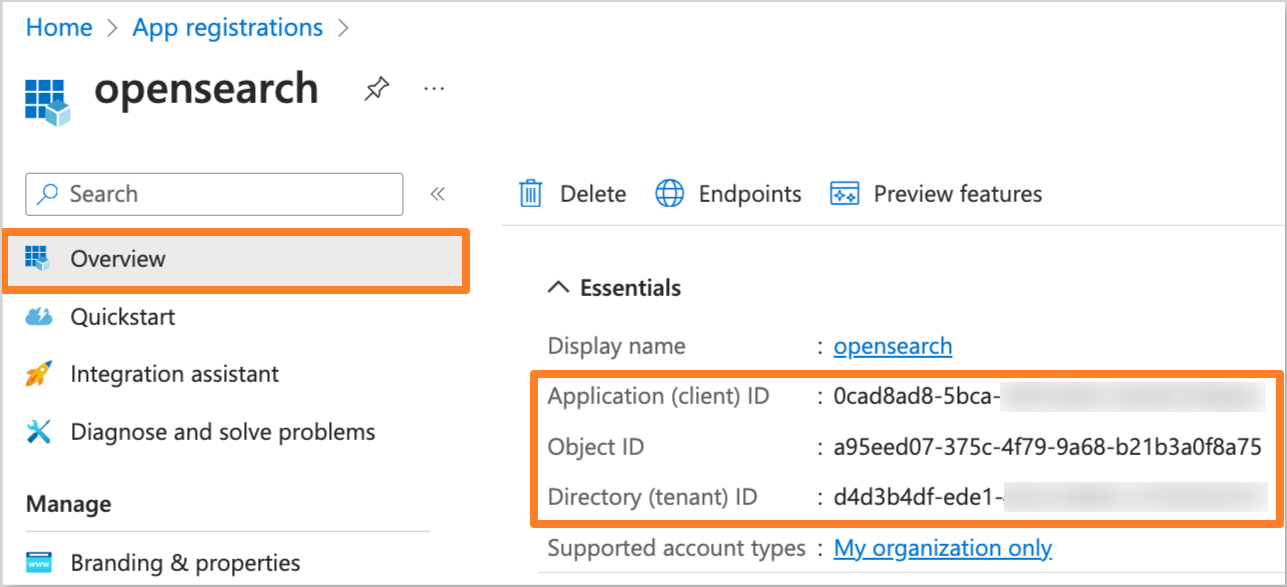
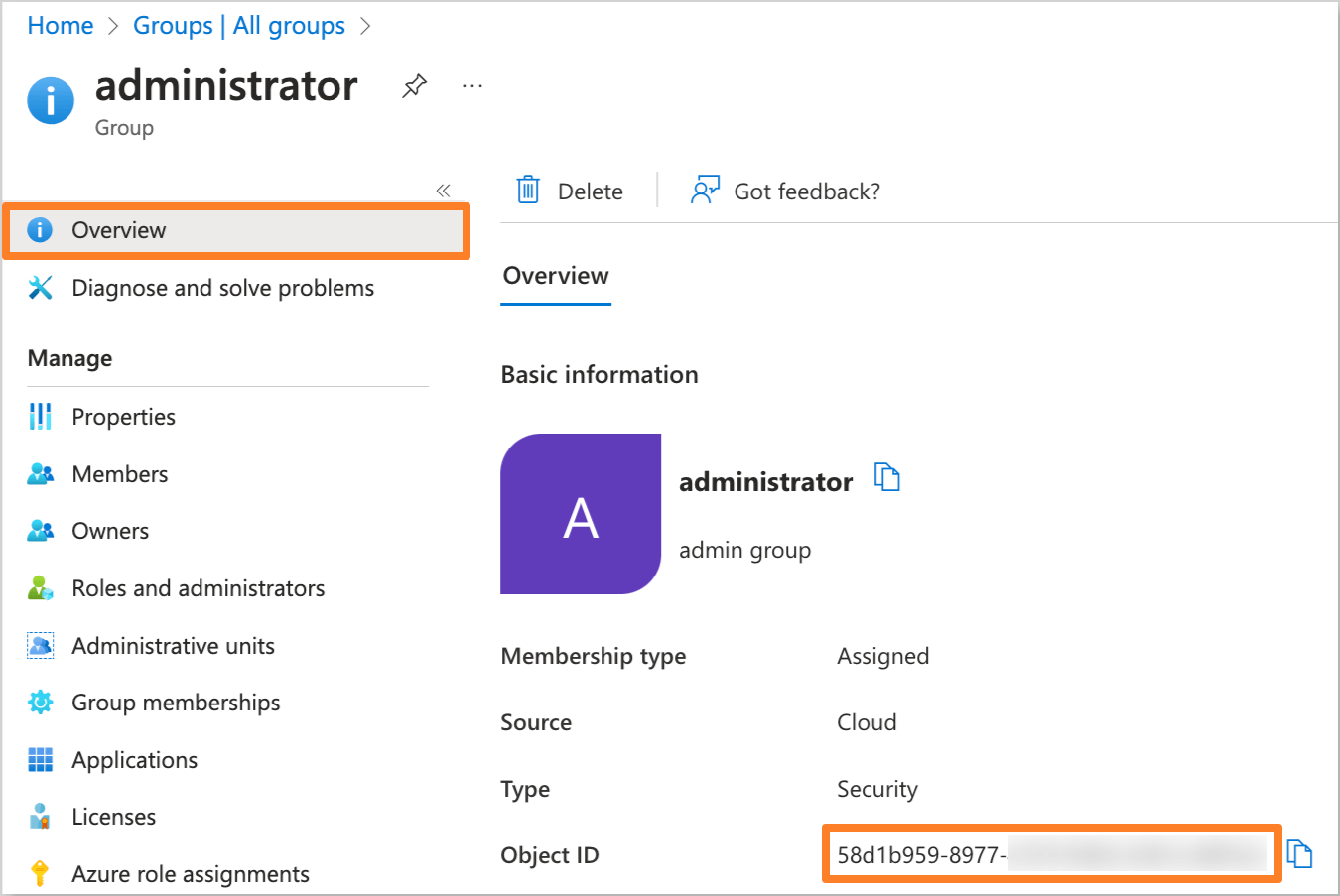
The Object ID can be found in the Overview section of the group in the Microsoft Entra Admin Center.
-
Navigate to the forked Cluster Add-Ons repository and locate the
values.yamlfile in theclusters/core/addons/opensearchdirectory:Update the
opensearchsection in thevalues.yamlfile with the following values:clusters/core/addons/opensearch/values.yamlopensearch:securityConfig:config:data:config.yml: |-config:dynamic:authc:openid_auth_domain:http_enabled: truetransport_enabled: trueorder: 1http_authenticator:type: openidchallenge: falseconfig:subject_key: preferred_usernameroles_key: rolesopenid_connect_url: https://login.microsoftonline.com/<Directory (tenant) ID>/v2.0/.well-known/openid-configurationopenid_connect_idp:enable_ssl: falseverify_hostnames: falseauthentication_backend:type: nooproles_mapping.yml: |-_meta:type: "rolesmapping"config_version: 2all_access:reserved: truebackend_roles:- "<Object ID of the Administrator group>"- "admin"description: "Maps EDP administrator role and internal admin role to all_access"logstash:reserved: truebackend_roles:- "logstash"description: "Maps log injection role to logstash. It might be logstash, fluent-bit, fluentd, ..."kibana_user:reserved: falsebackend_roles:- "kibanauser"- "<Object ID of the Developer group>"description: "Maps kibanauser and EDP developer role to kibana_user"kibana_server:reserved: trueusers:- "kibanaserver"edp_developer:reserved: falsebackend_roles:- "<Object ID of the Developer group in Microsoft Entra>"description: "Maps EDP developer role to view kube index"Replace the following placeholders with the actual values:
<Directory (tenant) ID>: The Directory ID of your Microsoft Entra Tenant.<Object ID of the Administrator group>: The Object ID of theadministratorgroup from the Microsoft Entra Admin Center.<Object ID of the Developer group>: The Object ID of thedevelopergroup from the Microsoft Entra Admin Center.
Update the
opensearch-dashboardssection in thevalues.yamlfile with the following values:clusters/core/addons/opensearch/values.yamlopensearch-dashboards:config:opensearch_dashboards.yml:server:auth.type: openidopenid:connect_url: https://login.microsoftonline.com/<Directory (tenant) ID>/v2.0/.well-known/openid-configurationbase_redirect_url: https://opensearch-dashboards.example.comclient_id: <Application (client) ID>client_secret: ${OIDC_CLIENT_SECRET}scope: openid profile emailheader: Authorizationverify_hostnames: falsetrust_dynamic_headers: trueReplace the following placeholders with the actual values:
https://opensearch-dashboards.example.com: The base URL of the OpenSearch Dashboards.<Directory (tenant) ID>: The Directory ID of your Microsoft Entra Tenant.<Application (client) ID>: The Application ID from the Microsoft Entra Application settings.
-
Update or create the
opensearch-dashboards-accountsecret with the Application Client Secret value:-
Using External Secrets Operator:
Be sure to update the AWS Parameter Store object path specified in the
clusters/core/addons/opensearch/values.yamlfile in theeso.secretNamefield with theusername,password,cookieandOIDC_CLIENT_SECRETvalues.AWS Parameter Store object{"opensearch-dashboard": {"username": "<Username>","password": "<Password>","cookie": "<Randomly generated cookie value>","OIDC_CLIENT_SECRET": "<Application Client Secret>"}} -
Manual approach:
Create the
opensearch-dashboards-accountsecret manually using the following template:opensearch-dashboards-account.yamlapiVersion: v1kind: Secretmetadata:name: opensearch-dashboards-accountnamespace: <namespace>type: Opaquedata:username: <Username>password: <Password>cookie: <Randomly generated cookie value>OIDC_CLIENT_SECRET: <Application Client Secret>
-
-
After updating the
values.yamlfile and creating theopensearch-dashboards-accountsecret, commit the changes to the repository and apply the changes with Helm or Argo CD. -
Navigate to the Microsoft Entra Application and add the Redirect URI in the Authentication section if you haven't done it before:
noteThe Redirect URI should be in the format
https://<OpenSearch Dashboard URL>/auth/openid/login.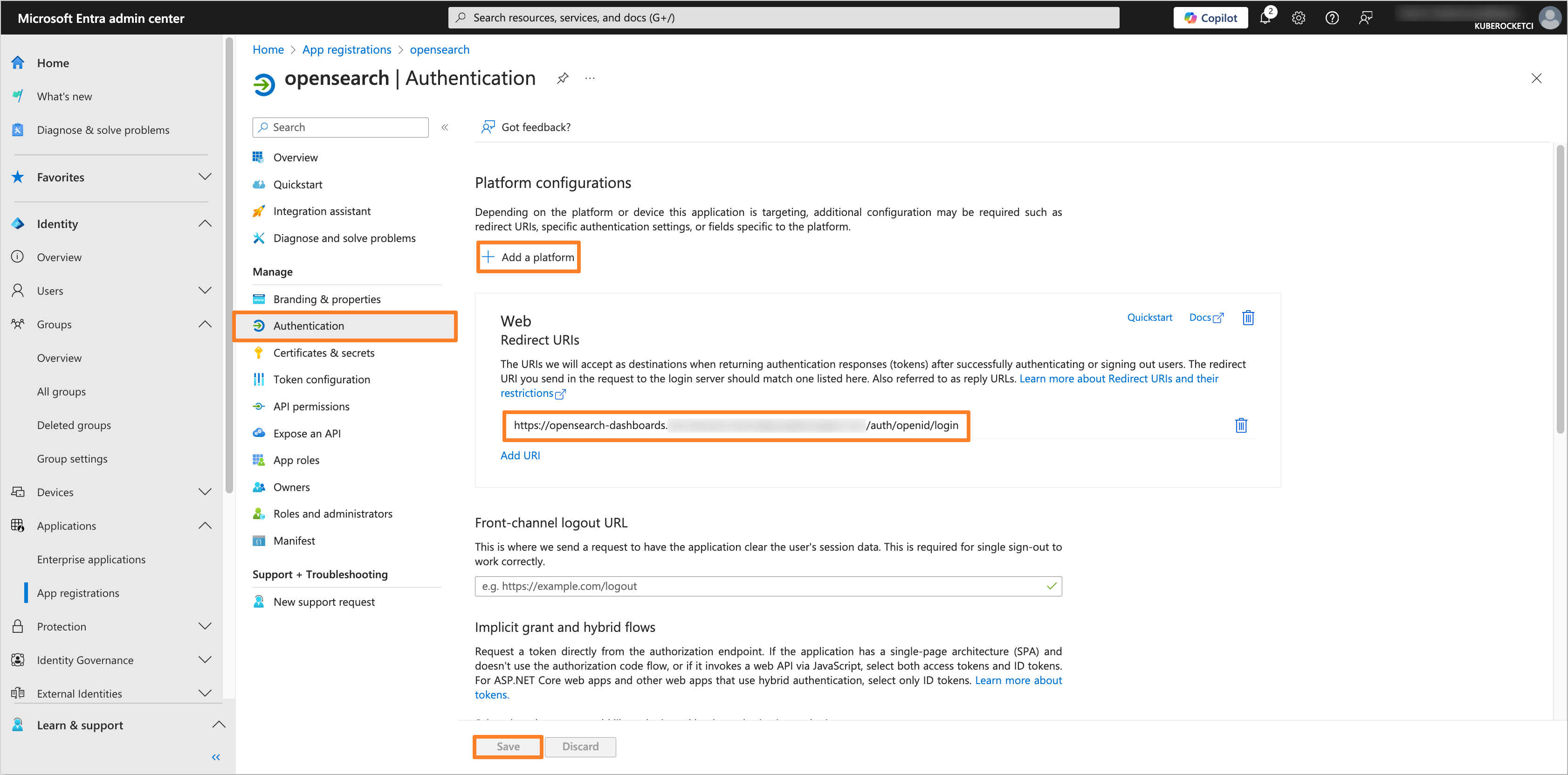
-
Verify that the OIDC authentication is configured correctly by logging in to OpenSearch using the Microsoft Entra credentials:
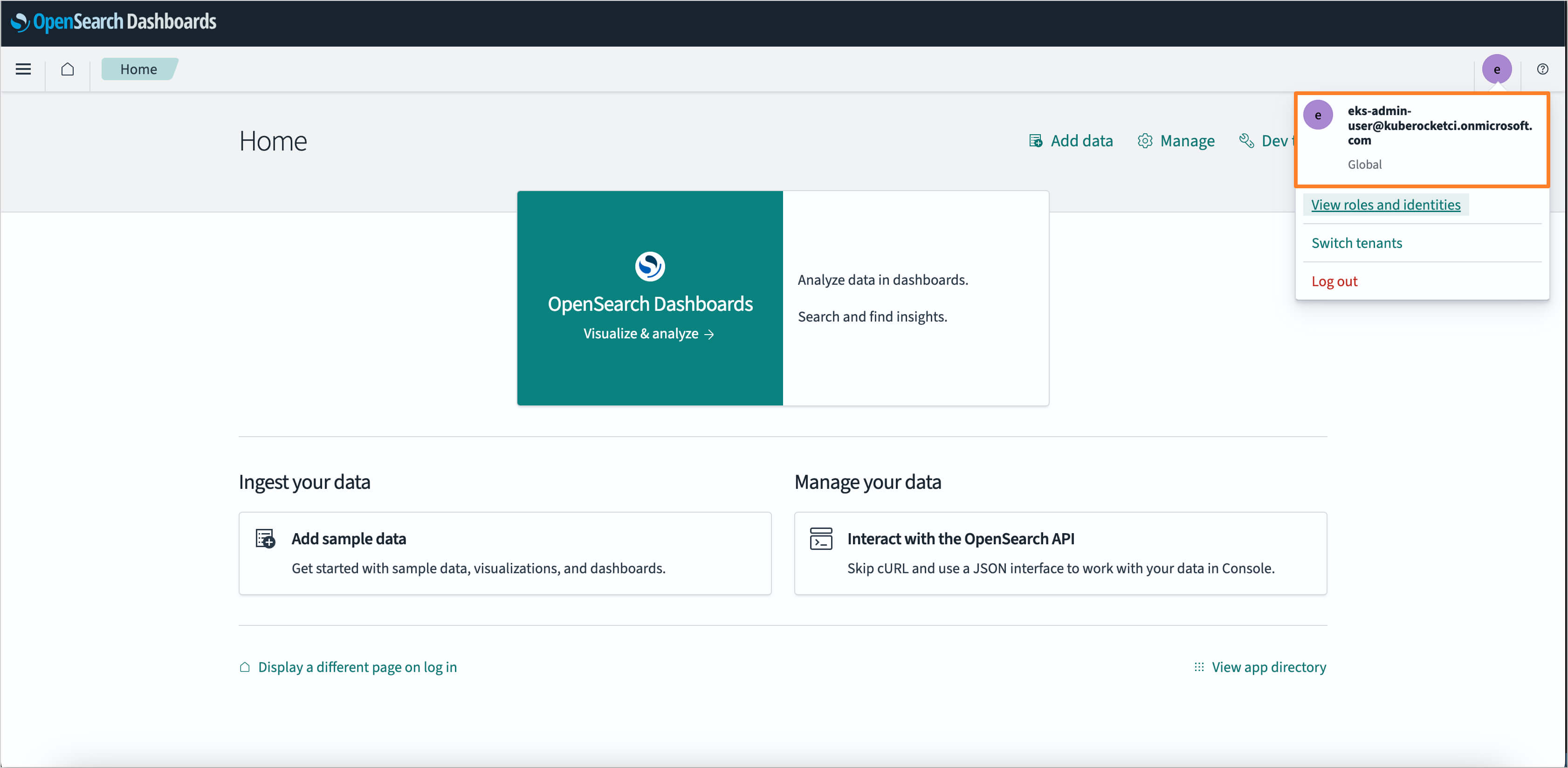
After completing these steps, OpenSearch will be configured with OIDC authentication using Microsoft Entra as the Identity Provider.