Portal OIDC Configuration
This page provides instructions for configuring the OIDC authorization for the KubeRocketCI portal, enabling the use of Single Sign-On (SSO) for authorization in the Portal. This configuration allows for centralized control of user access and rights from a single configuration point.
Prerequisites
Ensure the following values are set first before starting the Portal OIDC configuration:
-
realm_id= shared -
client_id= eks -
keycloak_client_key= keycloak_client_secret_key (received from:Shared realm->clients->eks->Credentials->Client secret)
The values indicated above are the result of the Keycloak configuration as an OIDC identity provider. To obtain these values, please refer to the guidelines on the Keycloak OIDC EKS Configuration page.
Configure Keycloak
To proceed with the Keycloak configuration, perform the following:
-
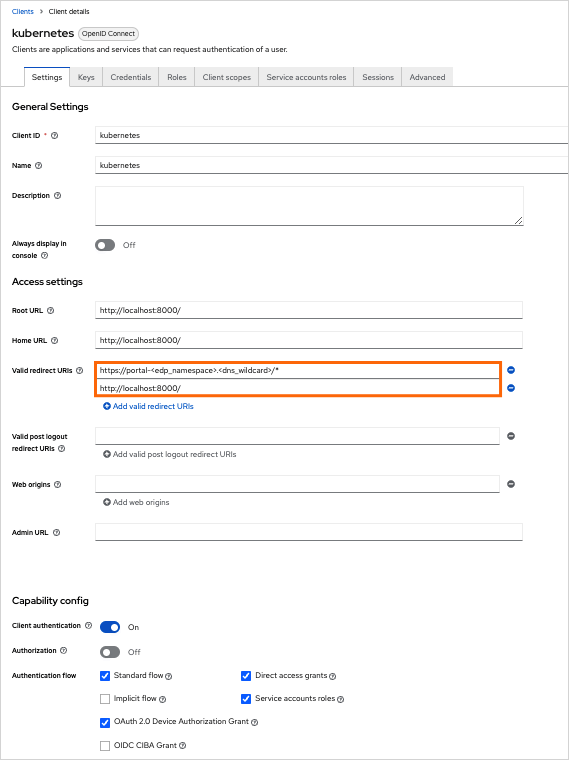
Add the URL of the Headlamp to the
valid_redirect_urisvariable in Keycloak:keycloak_openid_clientredirectUris:- "https://portal.<dns_wildcard>/*"- "http://localhost:8000/*"Make sure to define the following Keycloak client values as indicated:
-
Configure the Keycloak client key in Kubernetes using the Kubernetes secrets or the External Secrets Operator:
apiVersion: v1kind: Secretmetadata:name: keycloak-client-headlamp-secretnamespace: krcitype: OpaquestringData:clientSecret: <keycloak_client_secret_key> -
Assign user to one or more groups in Keycloak.
Integrate Portal With Kubernetes
Portal is integrated in Kubernetes in three steps:
-
Update the values.yaml file by enabling OIDC:
values.yamledp-headlamp:config:oidc:enabled: true -
Navigate to KubeRocketCI portal and log in by clicking the
Sign Inbutton: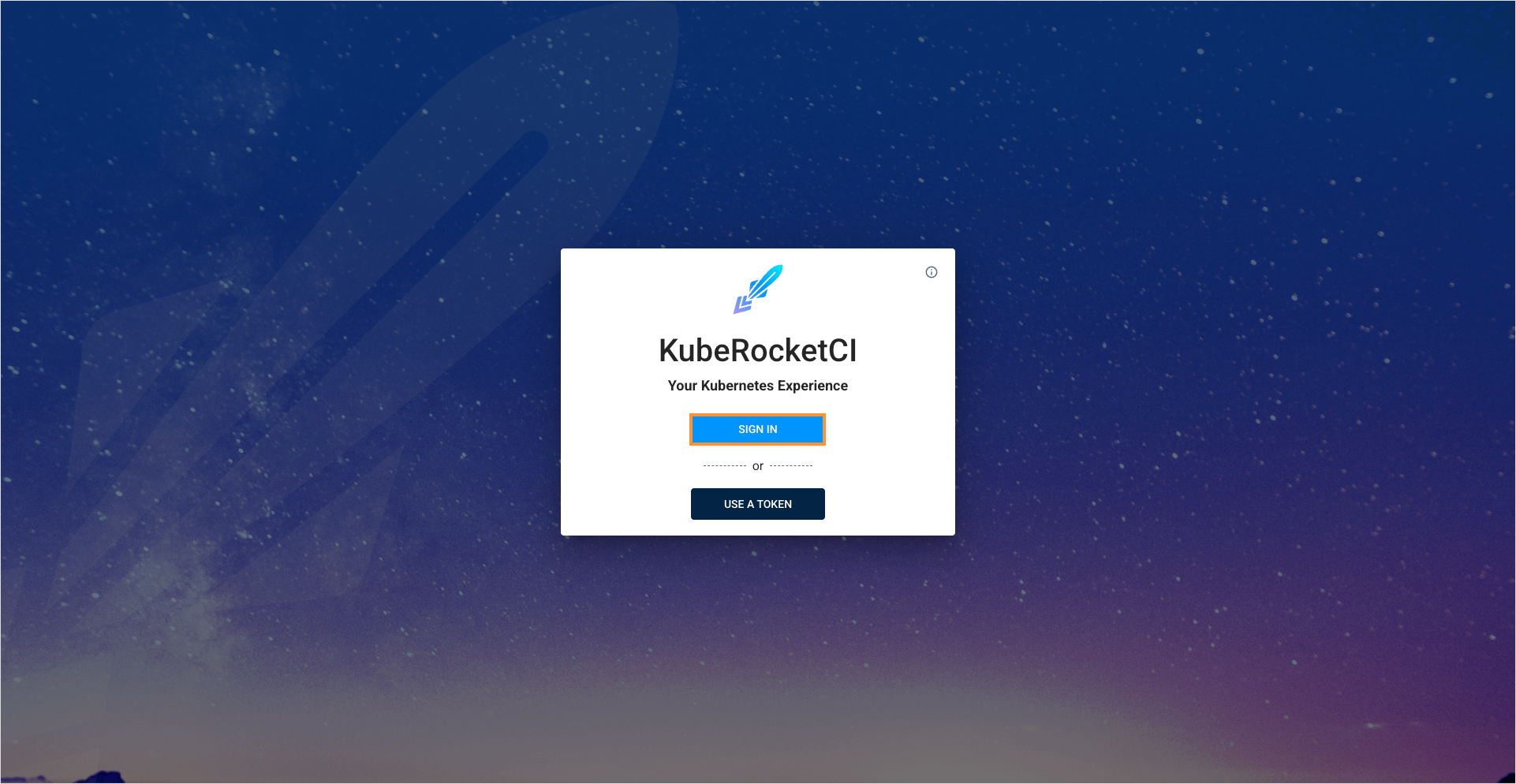
-
Upon logging in, ensure the namespace for KubeRocketCI is specified by clicking the Manage Namespaces button:
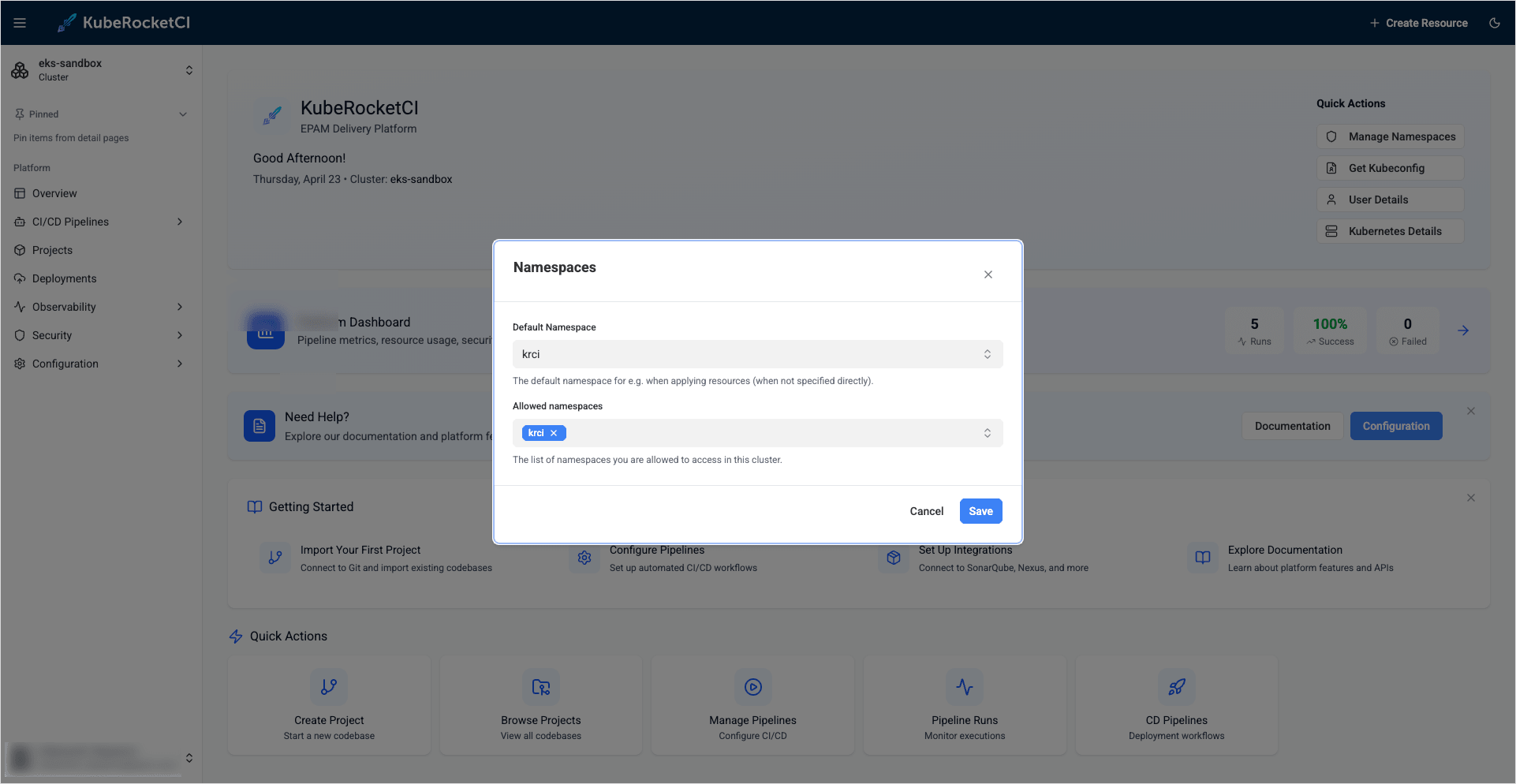
As a result, it is possible to control access and rights from the Keycloak endpoint.
Configure User Profile Picture
To enhance account personalization, a profile picture can be configured in the Portal using Keycloak. This requires setting up the Keycloak client scope with the necessary user attributes.
Follow the steps below to configure the user profile picture in Keycloak:
-
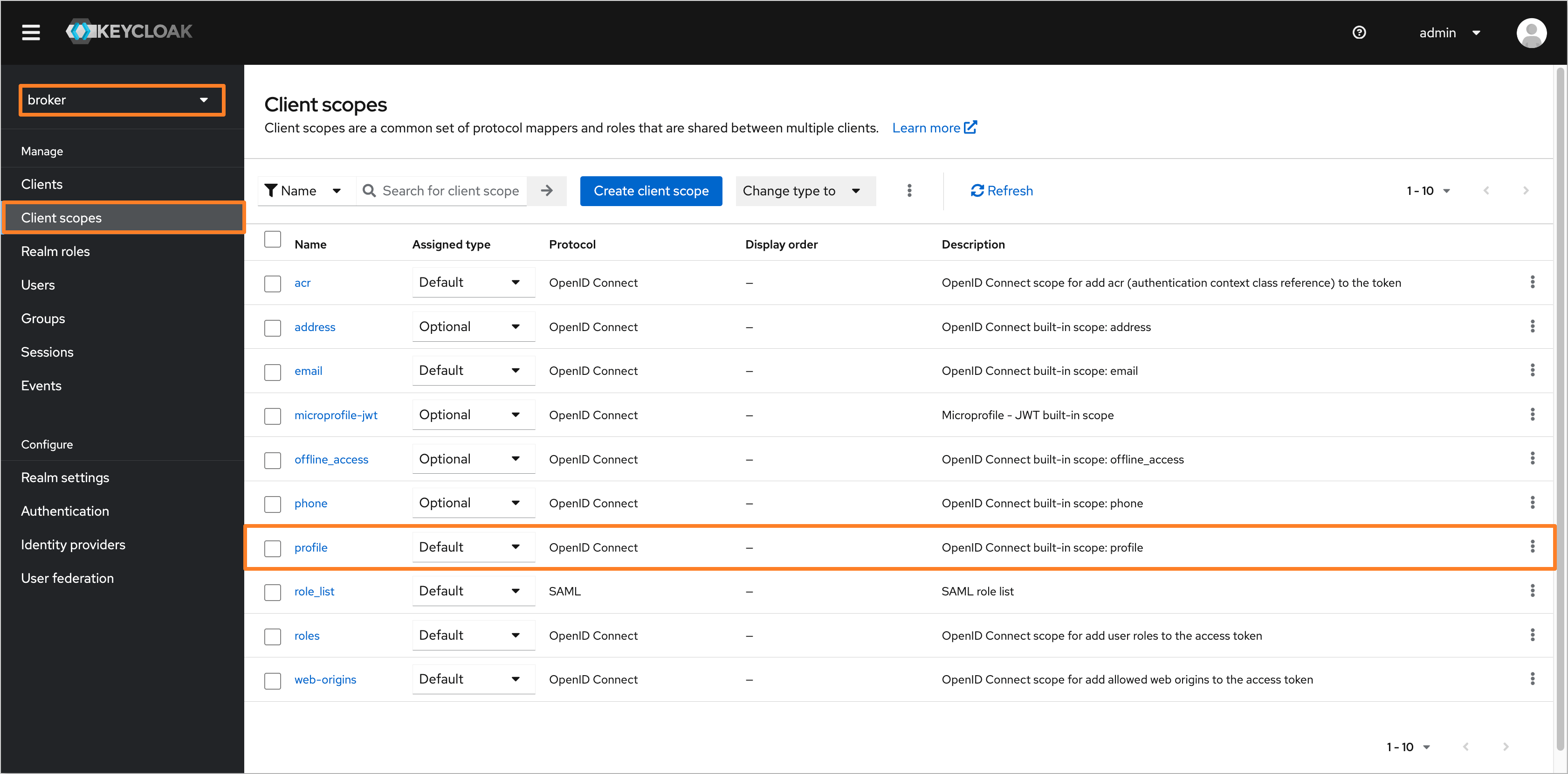
Open the Keycloak admin console and navigate to the Broker realm. In the left sidebar menu, select Client scopes and choose the profile scope:
-
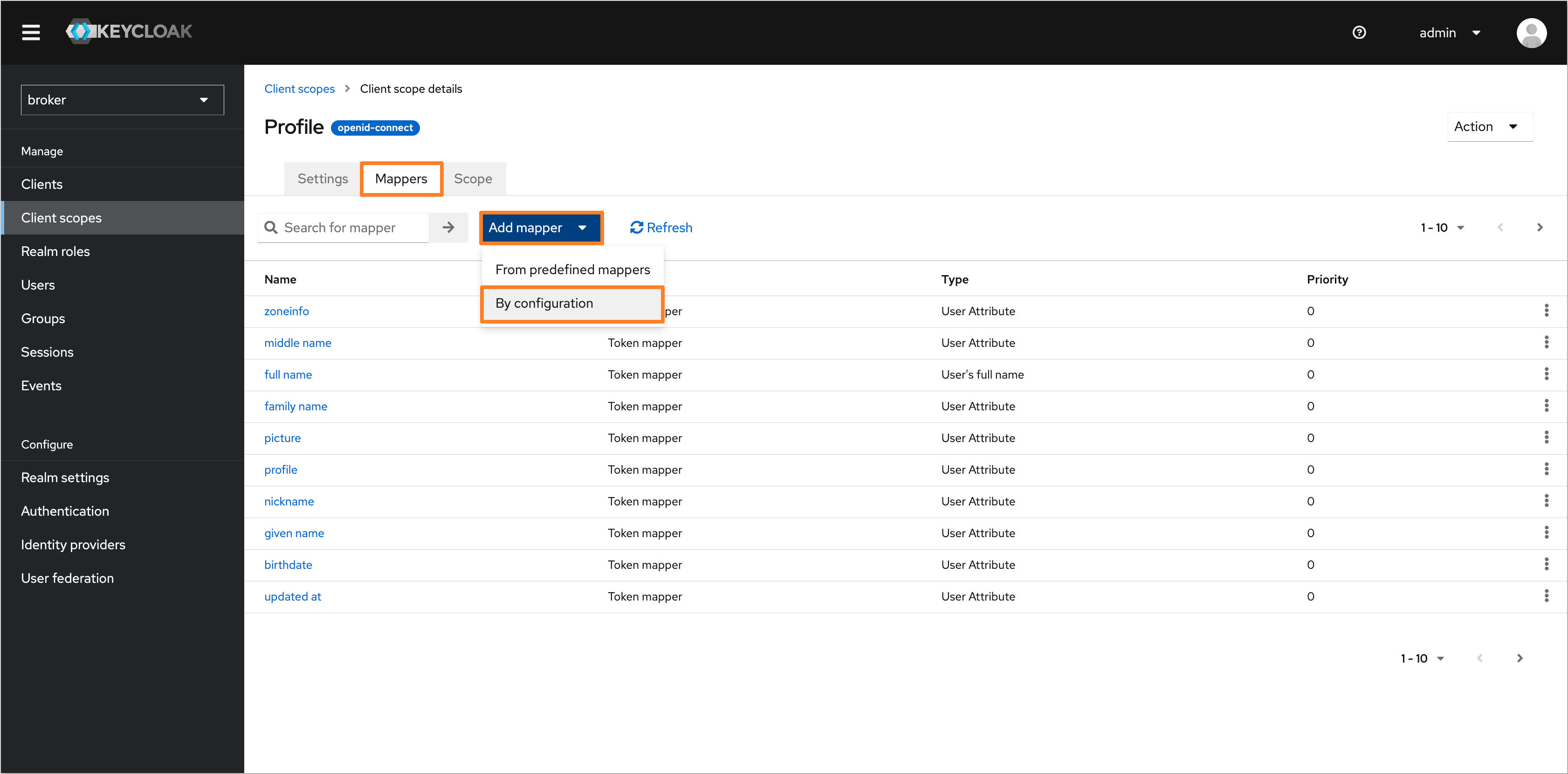
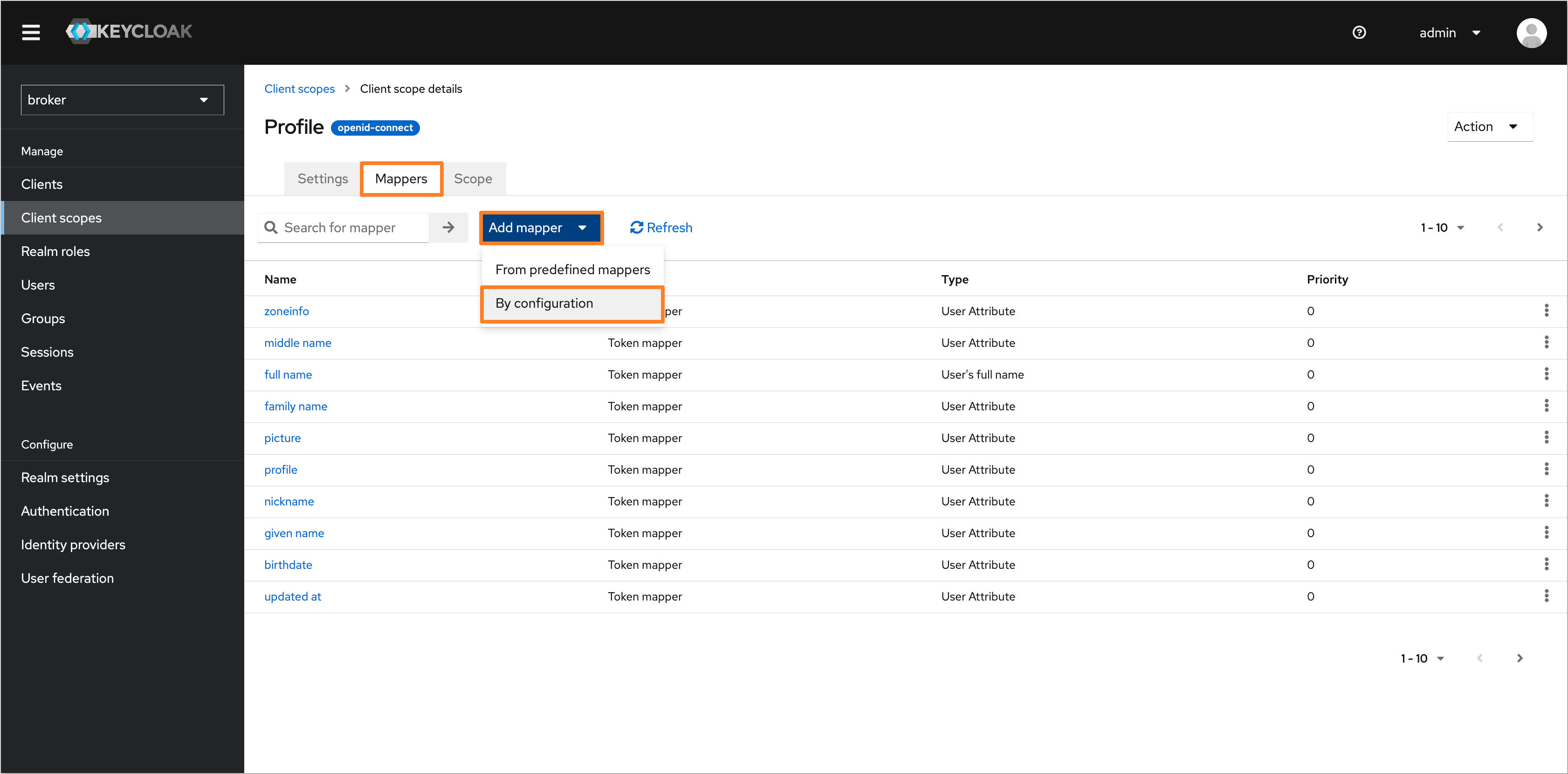
Navigate to the Mappers tab and ensure that the picture attribute is created. If the attribute is not present, click Add mapper button. In the dropdown menu, select By configuration:
noteIf the picture user attribute is already present, skip to step 5.
-
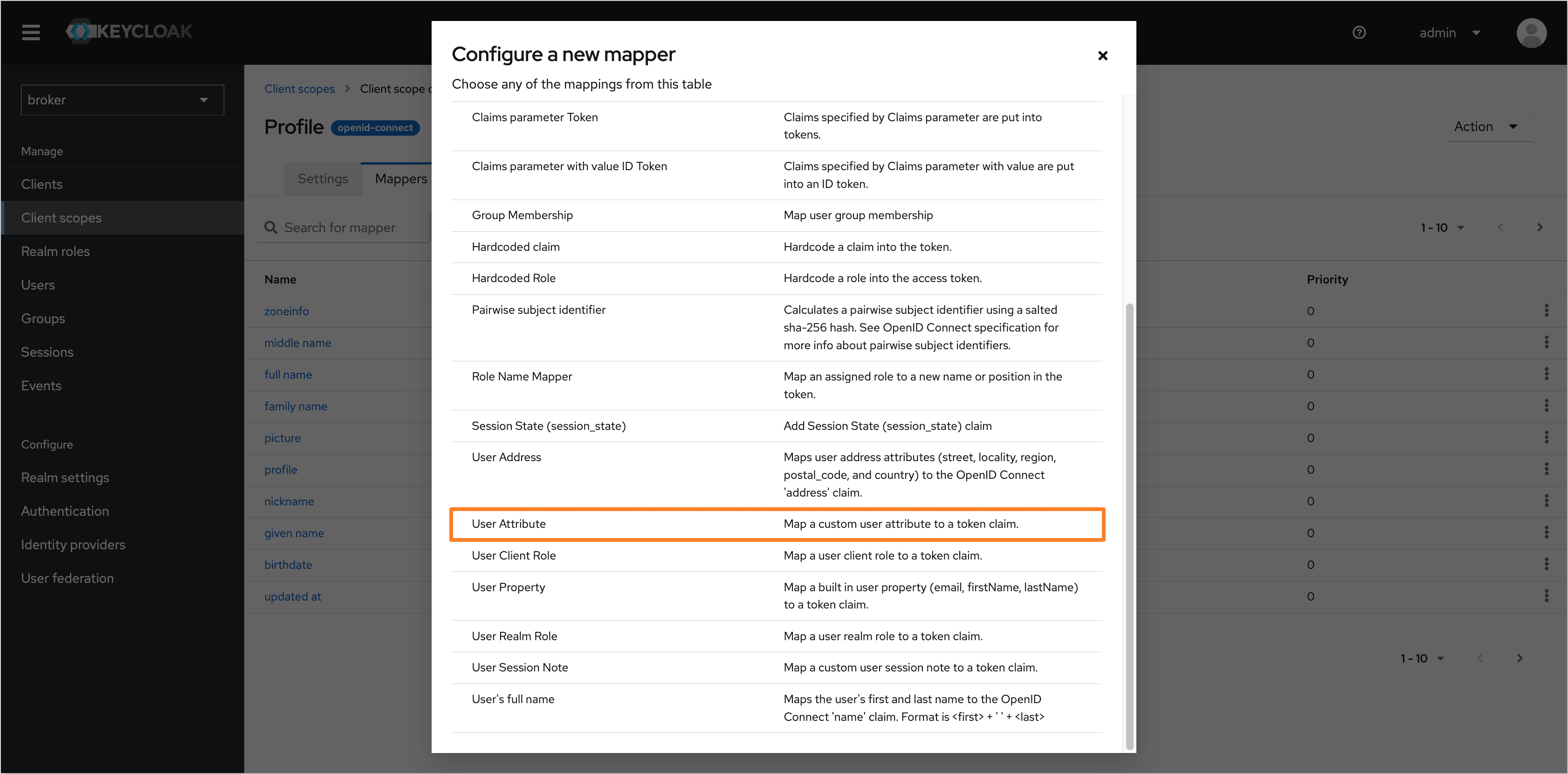
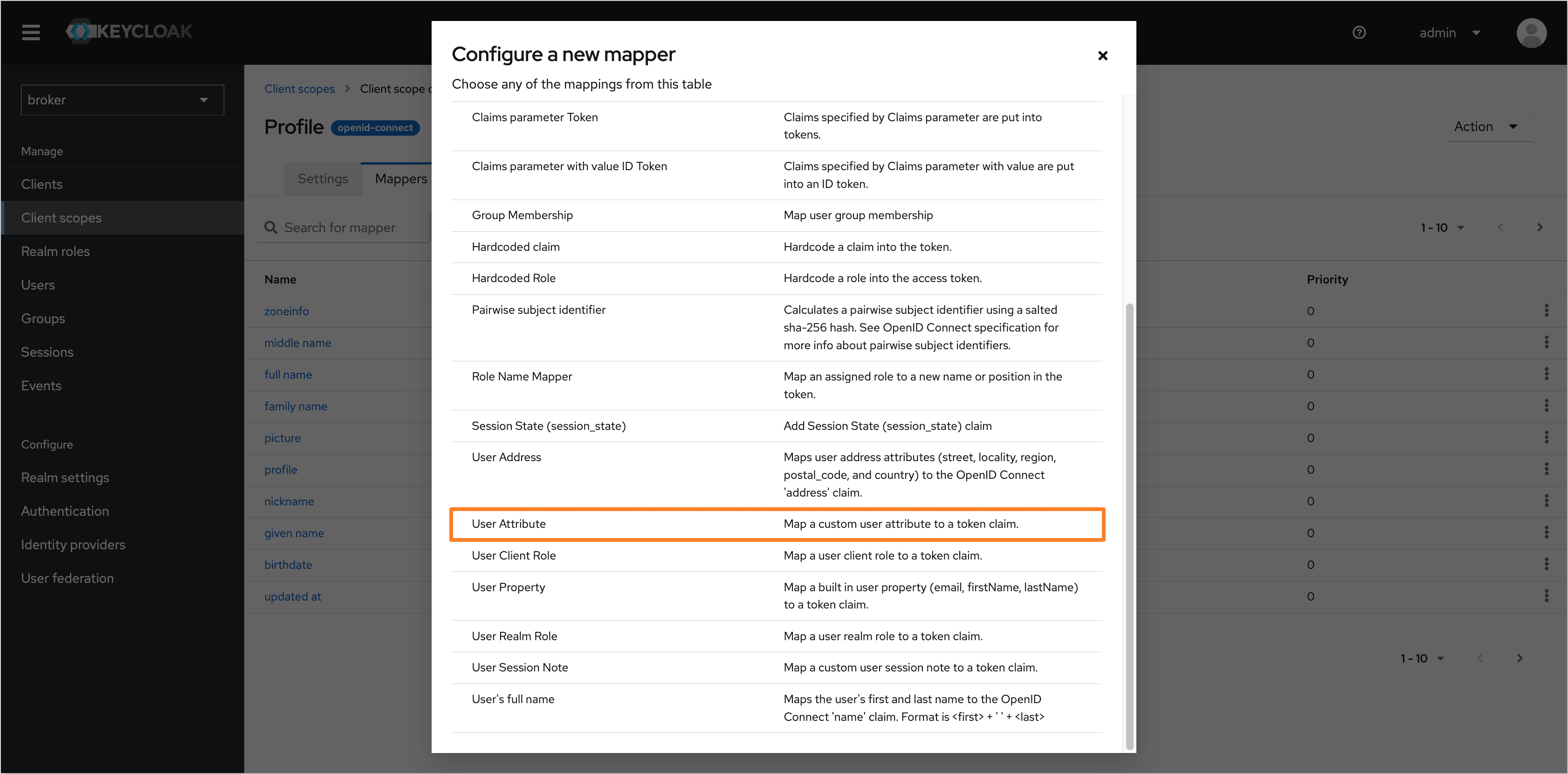
In the Configure a new mapper dialog, choose the User Attribute type:
-
Fill in the following fields to configure the user attribute:
- Name:
picture - User Attribute:
picture - Token Claim Name:
picture - Claim JSON Type:
String
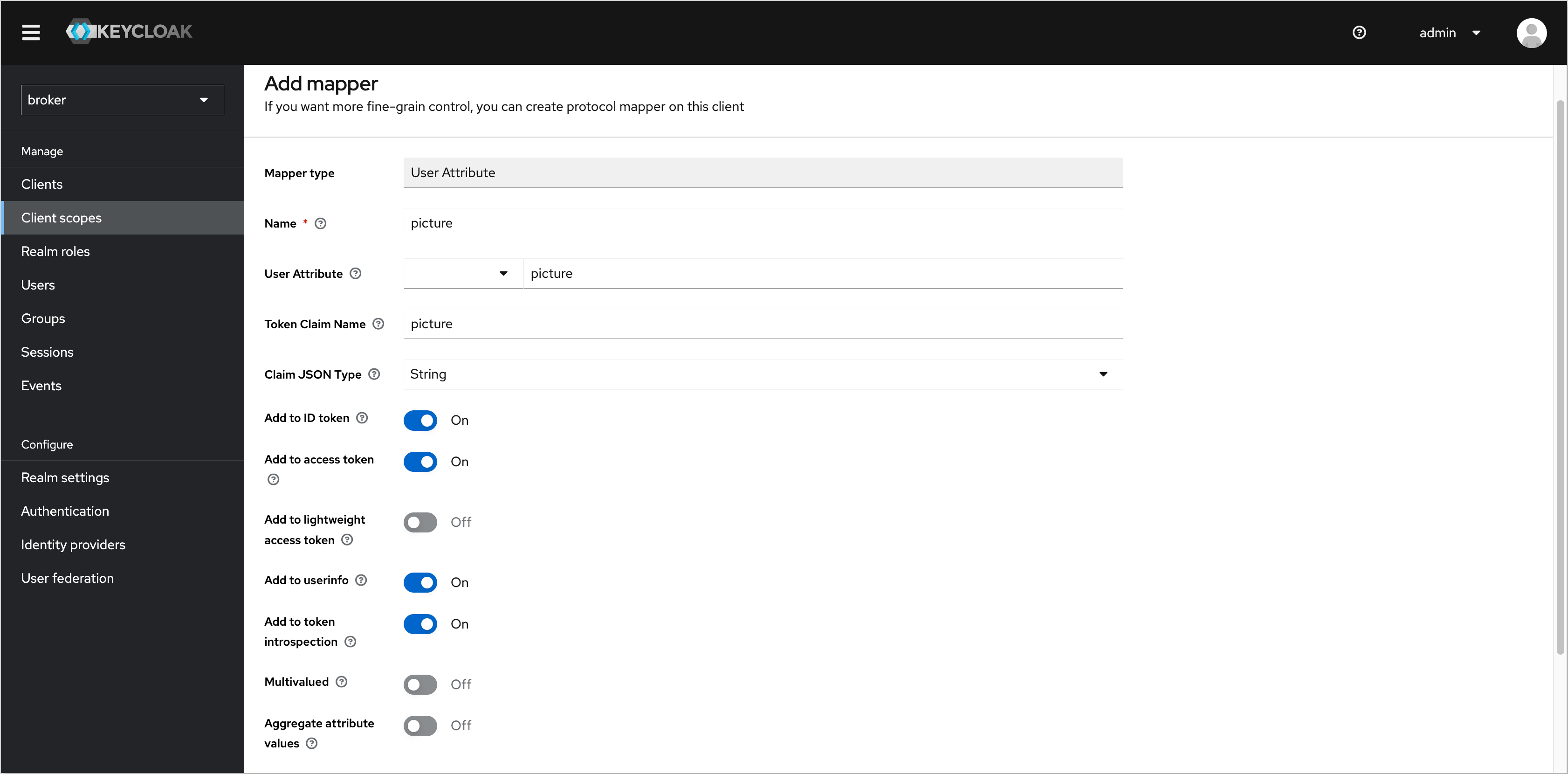
Click Save to apply the changes.
- Name:
-
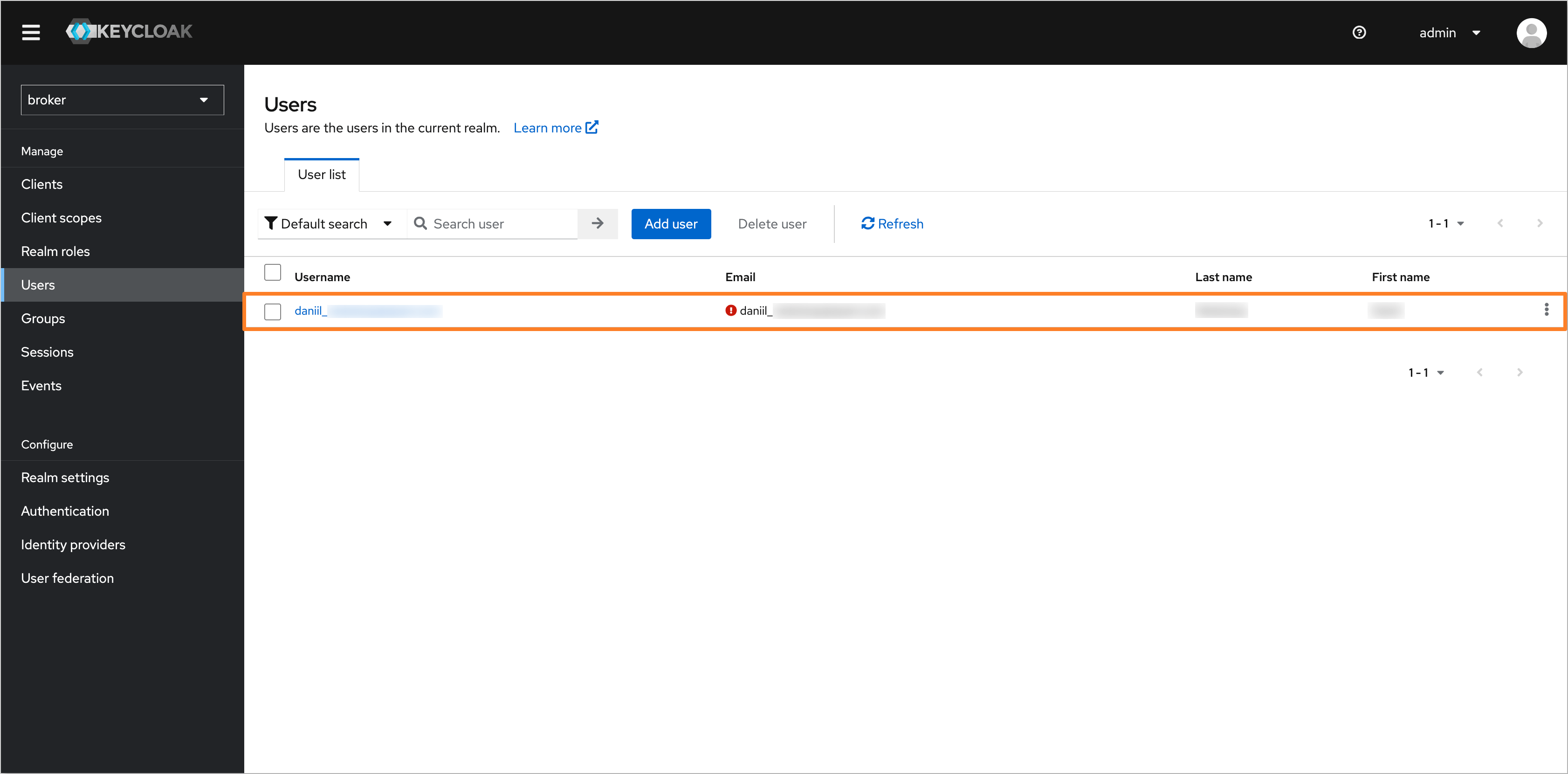
After configuring the user attribute, navigate to the Users tab in the left sidebar menu and select the user you want to set a profile picture for:
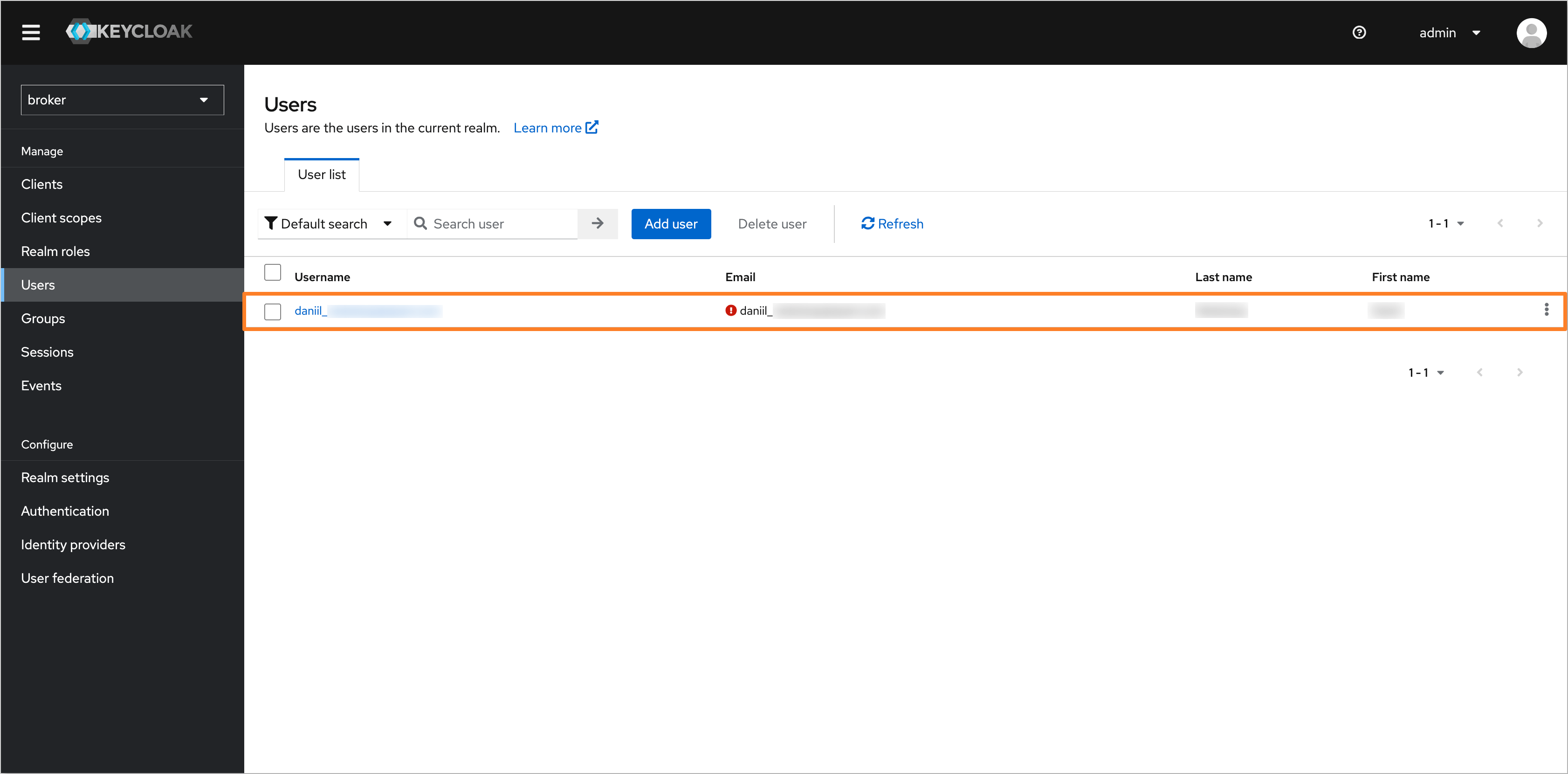
-
In the user profile, click Attributes and add the picture attribute with the URL of the desired profile picture:
noteThe profile picture URL should refer to an image accessible via a public URL.
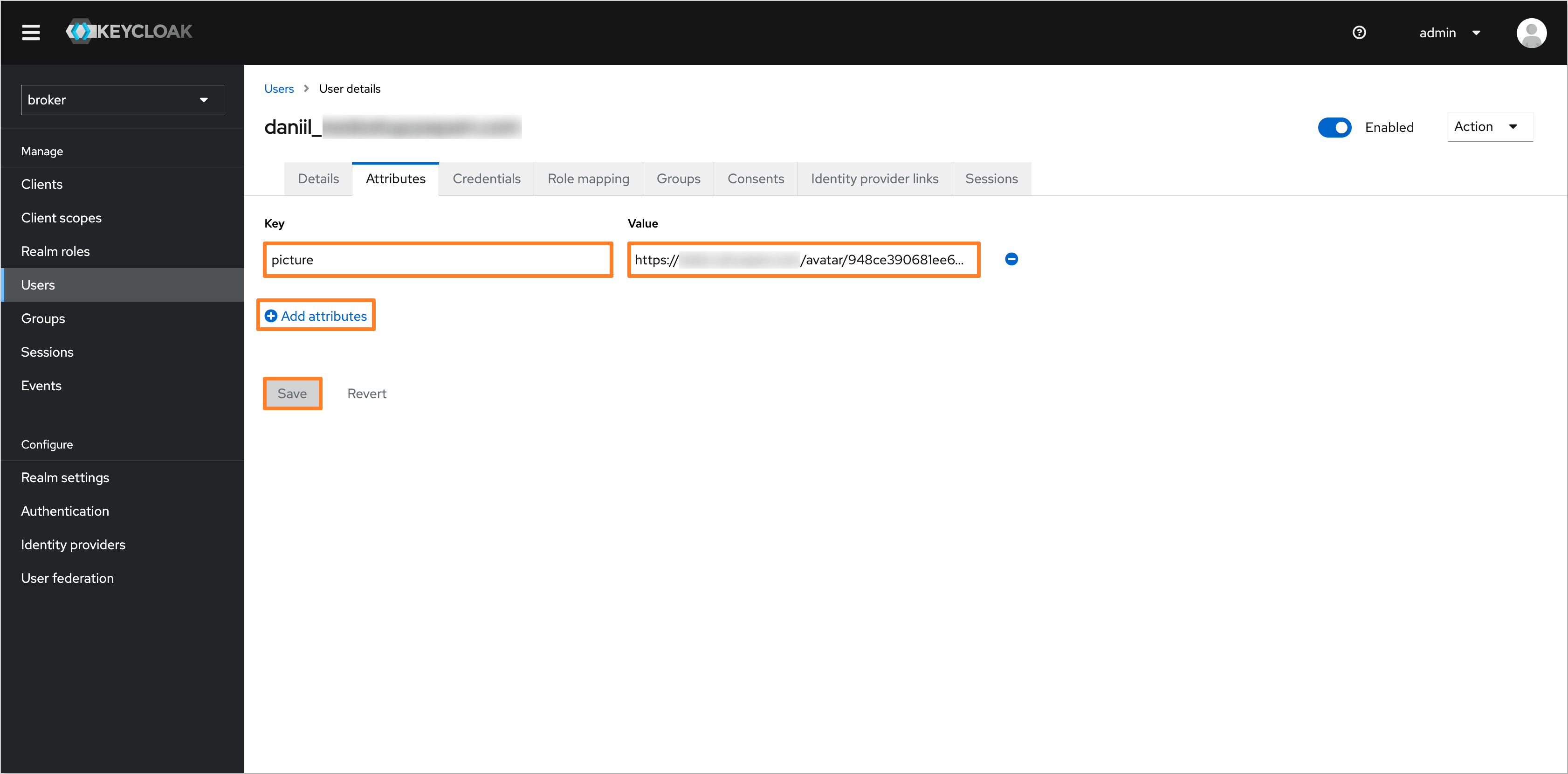
Click Save to apply the changes.
-
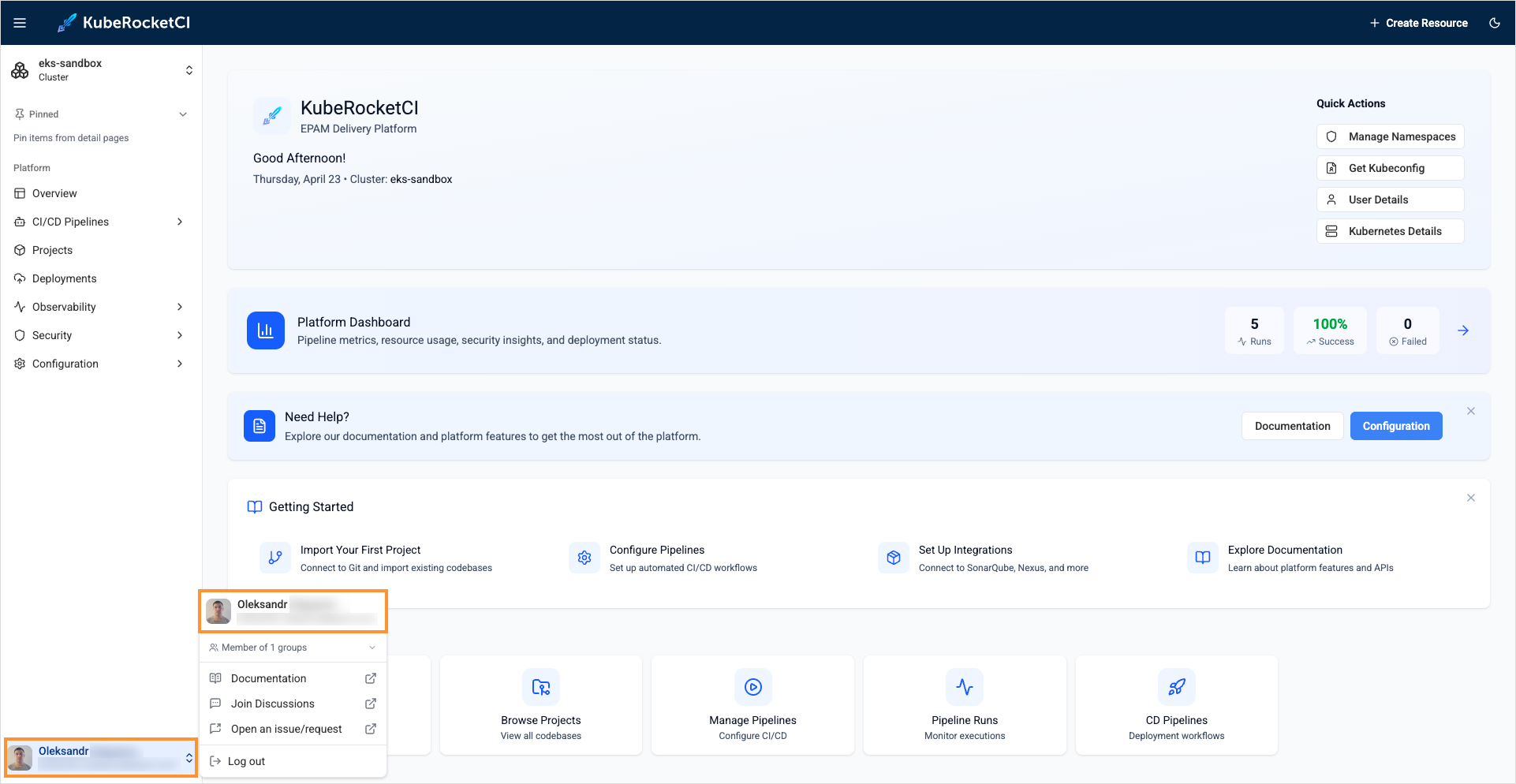
After configuring the user profile picture in Keycloak, the profile picture will be displayed in the KubeRocketCI portal:
Configure Default Namespace
After logging into the Portal, it is necessary to manually configure account settings like Default namespace and Allowed namespaces. To simplify this process, the default_namespace user attribute can be added to the user profile in Keycloak. This will ensure that the account settings are automatically configured during login.
Follow the steps below to configure the default_namespace user attribute in Keycloak:
-
Open the Keycloak admin console and navigate to the Broker realm. In the left sidebar menu, select Client scopes and choose the profile scope:
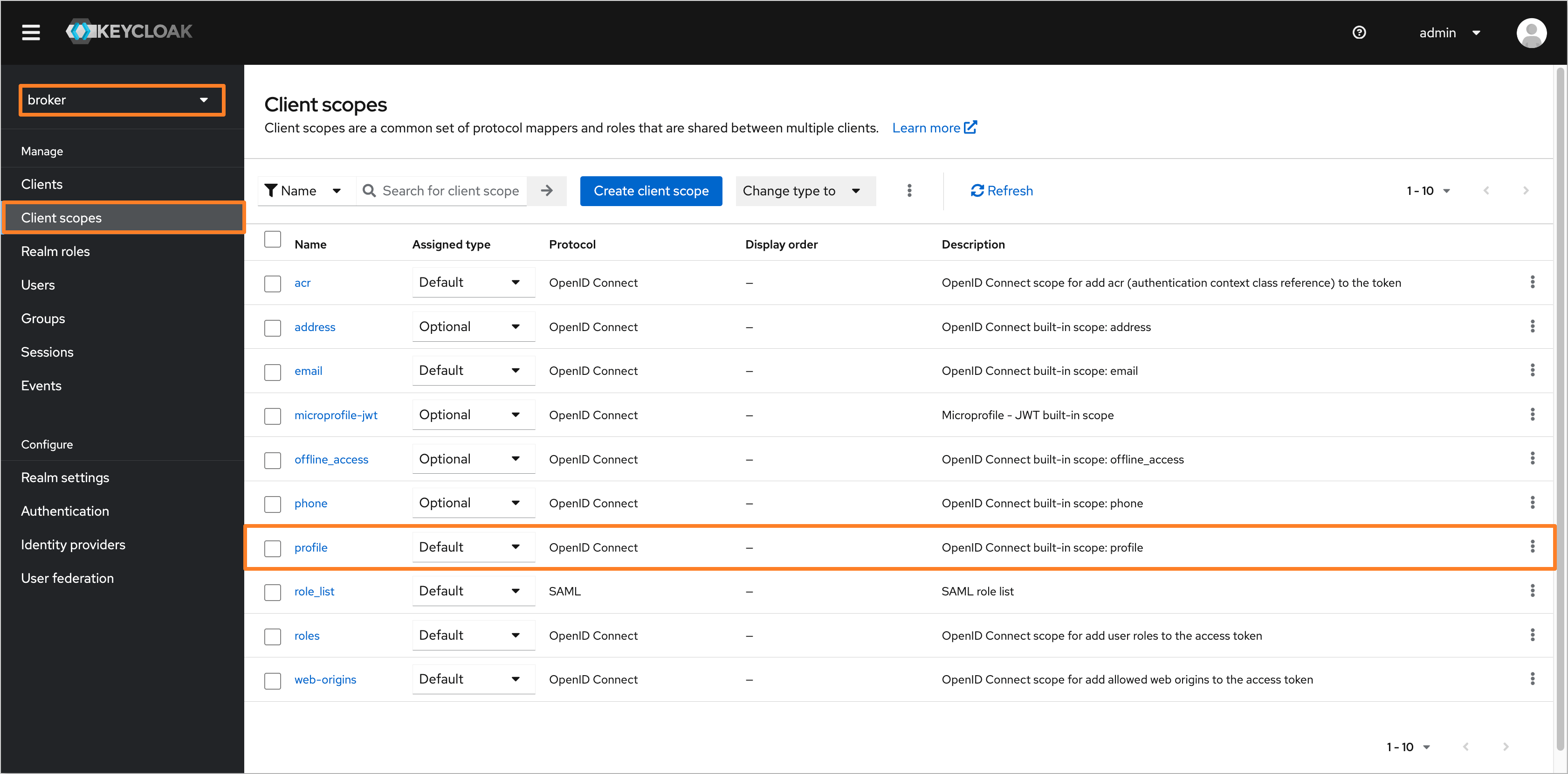
-
Navigate to the Mappers tab and click the Add mapper button. In the dropdown menu, select By configuration:
-
In the Configure a new mapper dialog, choose the User Attribute type:
-
Fill in the following fields to configure the user attribute:
- Name:
default_namespace - User Attribute:
default_namespace - Token Claim Name:
default_namespace - Claim JSON Type:
String
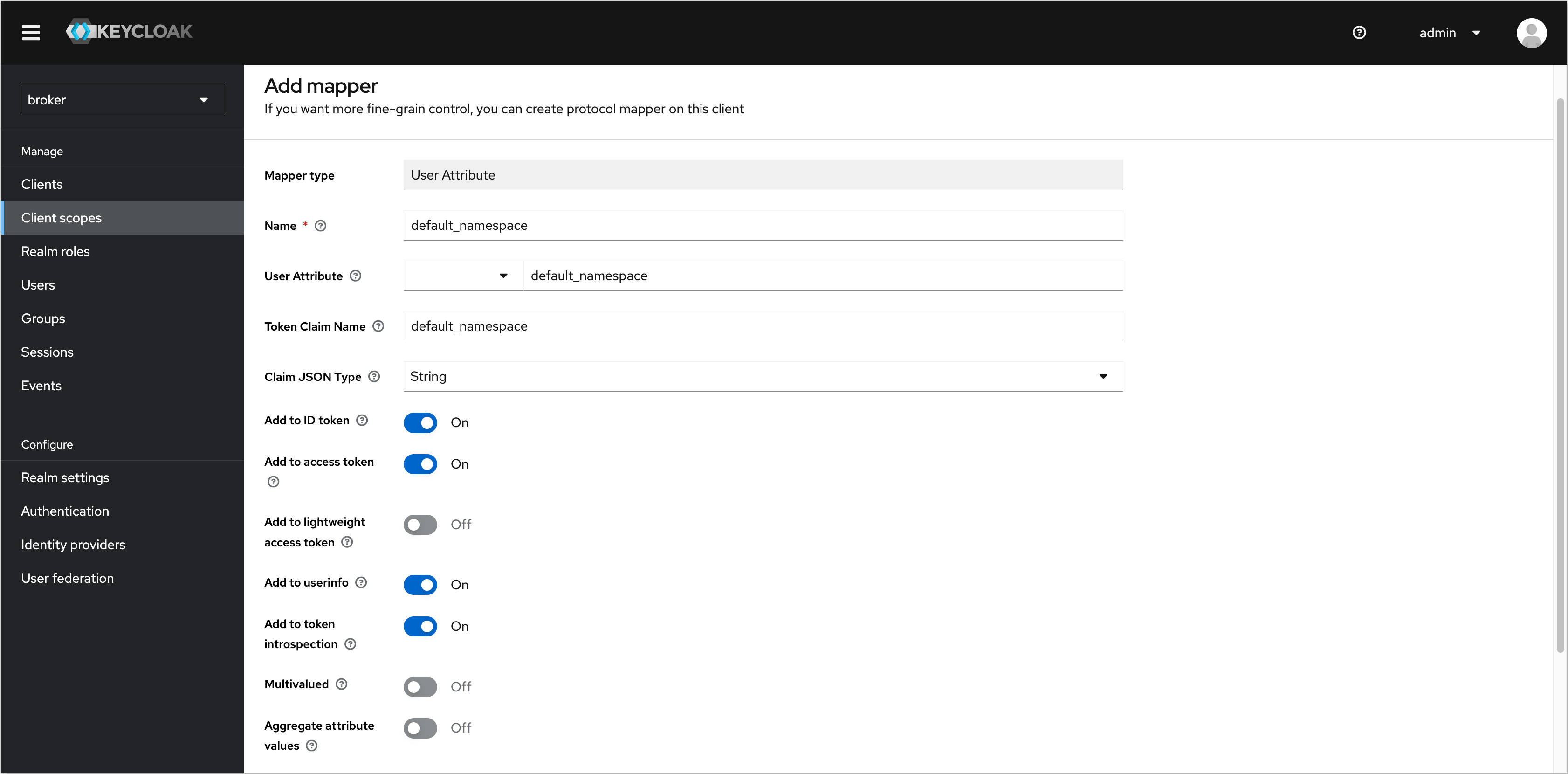
Click Save to apply the changes.
- Name:
-
After configuring the user attribute, navigate to the Users tab in the left sidebar menu and select the user you want to set a default namespace for:
-
In the user profile, click Attributes and add the default_namespace attribute with the name of the desired default namespace:
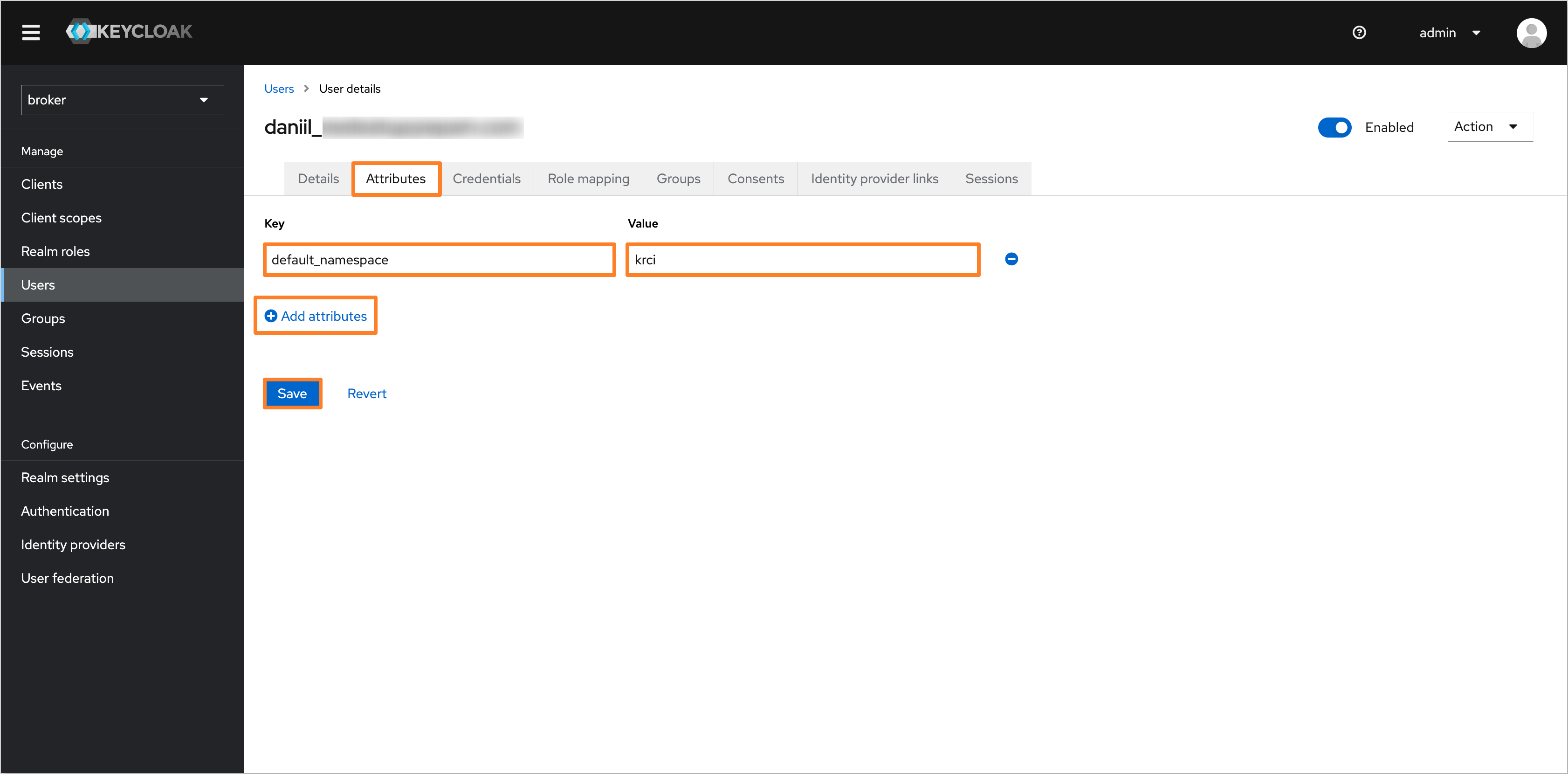
Click Save to apply the changes.
-
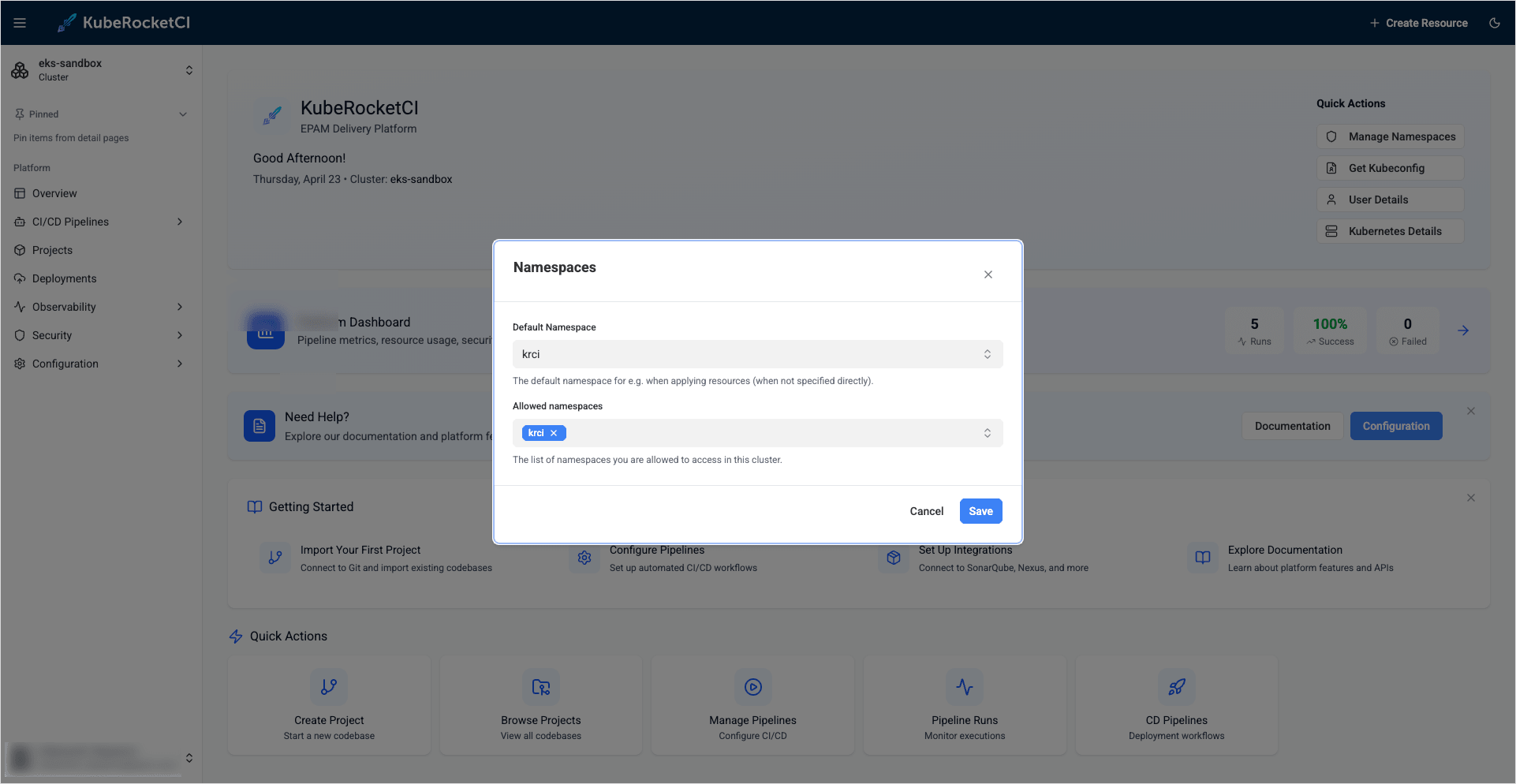
After configuring the user attribute with the default namespace in Keycloak, the account settings, such as the Default namespace and Allowed namespaces, will be automatically configured during login:
Changing the Lifespan of an Access Token
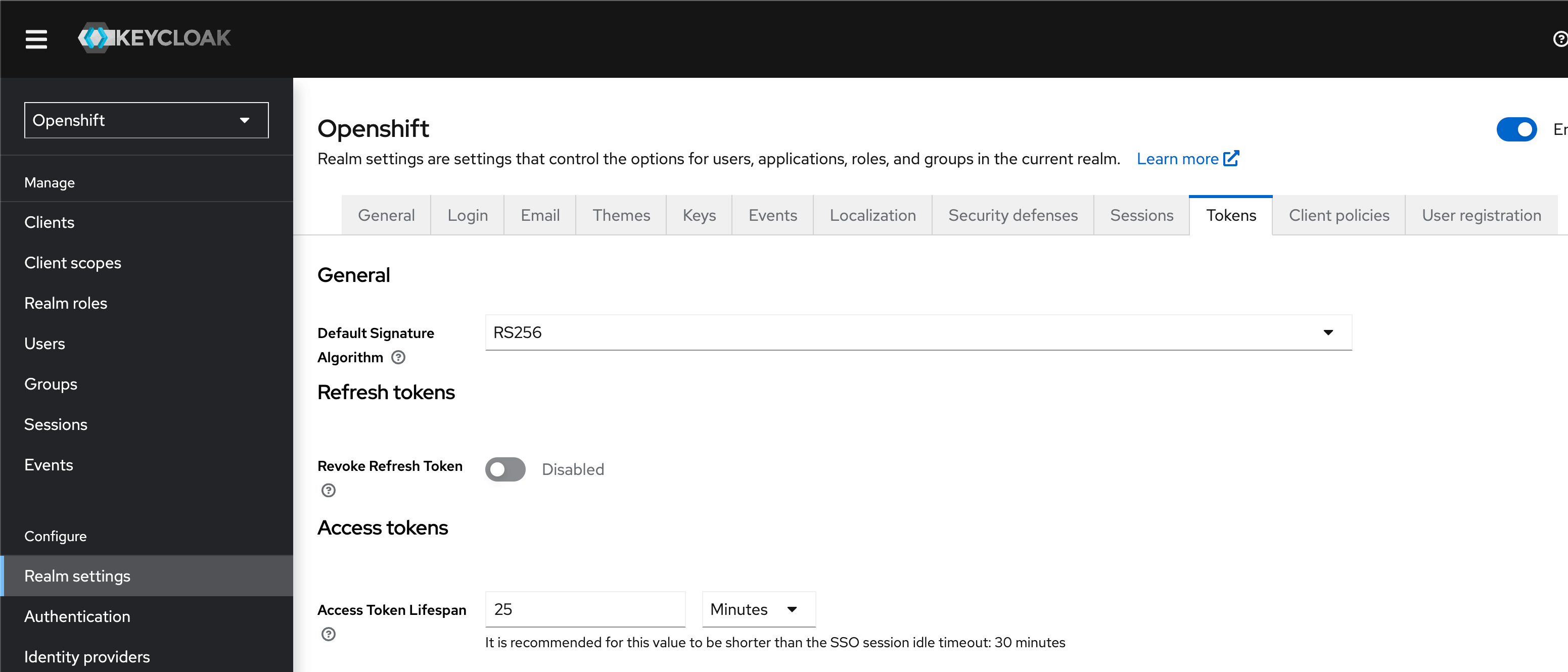
Change the Access Token Lifespan: go to your Keycloak and select Openshift realm > Realm settings > Tokens > Access Token Lifespan > set a new value to the field and save this change.
By default, "Access Token Lifespan" value is 5 minutes: